Every mobile phone has a special card called a Subscriber Identity Module. This is the challenge for a type of attack called SIM swapping which is becoming increasingly easier, thanks to leaks that associate email addresses and mobile phone numbers. In my latest post for Avast’s blog, I take a deeper dive into how this type of attack is pulled off, why it’s so popular, and steps that you can take to prevent it in the future.
Category Archives: wireless networks
The tale of the ProxyHam project
If you are trying to exfiltrate some data from a location and don’t want anyone to capture your source IP address, the best way to do that is to have an anonymous proxy router that can disguise your real IP address behind its own. Such devices have existed for many years, but Ben Caudill has come along with a new version that he calls ProxyHam.
It works by connecting your network to the router’s Wi-Fi bridge, and in turn, it routes your data over a 900 MHz radio to a distant computer with a hi-gain antenna. The antenna picks up the signal and masks your IP address, keeping you at a distance, supposedly safe from detection.
Caudill was scheduled to speak at the DEF CON security conference earlier this month to show off his innovation, under the heading called the Anonymous Proxy Router Project. The presentation was supposed to demonstrate how to build an anonymous proxy router for a couple hundred bucks out of commonly available parts. Sadly, the session was canceled in July; the principles are mum as to the cause. Units that were built by Caudill’s company Rhino Security have been destroyed and aren’t for sale, and the source code is no longer available.
One reasonable explanation for why the talk was canceled is because it’s likely that ProxyHam breaks the law. First, FCC Part 97 has a prohibition against using encryption — such as the SSH or HTTPS protocols that you most certainly would be using with ProxyHam — over the 900 MHz band radio signals. Then, depending on where you place your ProxyHam or its equivalent, you could be doing something unauthorized on the target network, which comes under the Computer Fraud and Abuse Act.
Speculation about the router and the talk has run rampant, and some have noted that this mysterious cancellation all but ensures that Caudill and his anonymous proxy router will be the star of DEF CON — without ever even being demonstrated. “Ben Caudill used some routers and a Raspberry Pi to hack the media,” Brian Benchoff wrote on Hackaday. “If that doesn’t deserve respect, nothing does.”
Enterprise Impact of the Router
Certainly, the idea behind ProxyHam isn’t going away, and various folks around the Internet have stepped up to the challenge. I found three sources on how to build a similar version of the router. Benchoff covered the task for Hackaday, and an alternative anonymous proxy router was suggested by Samy Kamkar via TechWorm. And there is a third post from Robert Graham of Errata Security that shows yet another way to construct the device. All three versions cost about the same and have about the same minimal level of skill required to assemble the various parts.
This means that no matter what the motivations behind ProxyHam and its peers, enterprise IT managers should be on notice. They must be aware that these kinds of devices could be operating over their networks; it is only a matter of time.
The best defense is to make sure you tune your intrusion prevention filters. You can also use other tools to monitor what kinds of data leave your network. If you don’t have any outbound networking monitoring in place, now is the time to consider implementing such a tool. The ProxyHam router isn’t the only way data can be sent off-site: A simple connection to a personal Google Drive account is a lot less work and may be just as effective. But this issue is certainly worth more consideration because of the sheer impact it could have.
A short history of wireless messaging
As part of my tripping down memory lane and reading my archive, I naturally came across the dozens of articles that I have written over my career on wireless messaging. It made me think about how the industry has evolved so quickly that many of us don’t even give this technology a second thought — we just expect it to be part of our communications package.
Now our smartphones have multiple messaging apps: Email, SMS, What’s App, Skype, AOL IM, and Apple’s iMessage, just to name a few of them that are on my phone. We flip back and forth from one to the other easily. When you add in the social networks’ messaging features, there are tons more.
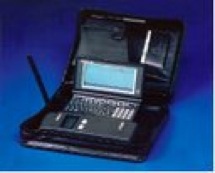 My first brush with wireless messaging was when Bill Frezza stopped by my office and gave me one of his first prototypes of what would eventually turn into the BlackBerry. It was called the Viking Express, and it weighed two pounds and was a clumsy collection of spare parts: a wireless modem, a small HP palmtop computer running DOS, and a nice leather portfolio to carry the whole thing around in.
My first brush with wireless messaging was when Bill Frezza stopped by my office and gave me one of his first prototypes of what would eventually turn into the BlackBerry. It was called the Viking Express, and it weighed two pounds and was a clumsy collection of spare parts: a wireless modem, a small HP palmtop computer running DOS, and a nice leather portfolio to carry the whole thing around in.
The HP ran software from Radiomail Corp. The company was one of the first to understand how to push emails to wireless devices. Its innovations were never patented due to the philosophy of its founder, Geoff Goodfellow. Ironically, after Research in Motion, the company behind the Blackberry, went on to become one of the more litigious computer vendors, it had to pay $615 million to obtain the rights for patents for its device.
Now wireless has gotten so fast, it can be faster than wired connections. Cisco’s latest networking report predicts that Internet traffic will carry more wireless than wired packets in a few years. And we have come full circle: with new desktop Macs, Apple has gone a bit retro on us. Now you can access iMessage from your desktop, which is great for those of us that want to type on regular keyboards, inside of with our thumbs or use Siri to compose messages.
So for those of you that don’t recall where we have been, I have posted the original articles that I wrote about some of the early wireless messaging apps for some perspective on my blog. Here are some links to them.
Review of smart pagers for Computerworld (1998)
Back then, BlackBerries weren’t available, and Motorola ruled the roost. Pagers were in transition from simple one-way devices that would just display numerals to more interactive messaging devices. However, they were pretty unsatisfying: The one-way pagers worked because they were tiny, their batteries lasted forever, and they could be used by anyone including my nine-year old. The smarter devices were harder to use, they aet batteries for lunch, and they didn’t always work without some specialized knowledge.
Evaluating wireless web technologies (2000):
Back then, I gave up my laptop and tried to use just a smart(er) phone and borrowed PCs when I traveled. There were some early apps back then that could actually work.
Supporting PDAs and wireless devices on your corporate network (2001):
The first messaging device to gain traction was the Palm Pilot, but we also had the Pocket PC too. This article was a piece of custom content for CDW that reviewed all the options available back then. For cellular data, you needed add-in radio cards.
The joys of wireless messaging (2003)
How about AOL’s IM running on a Palm i705? That was a pretty slick device, as this article can attest to.
Don’t buy a Treo 700w (2006):
Remember the Treo? I still have one somewhere in my closet. They were a combination of a phone and a Palm Pilot. Back then I wrote: “the Treo isn’t as cool as the Sidekick, doesn’t do iTunes like the Rokr, and isn’t as addicting as a CrackBerry.”
Sidebar conversations are here to stay (2009):
It isn’t just texting during driving, but texting while doing something else that is at issue.By 2009, the notion of having a side conversation using a wireless device was very common.
What is your favorite wireless messaging device or app from the past?
Picking the right mobile device management tool for your enterprise
One of the consequences of bringing your own device to work is in having to keep the work-related files on it secure once it enters the enterprise. This can be a challenge, and a dozens of vendors are now wrapping themselves in the trendy category of “mobile device managers” or MDMs. But trying to understand whether these products help secure the device, the user, the applications or the various files stored on each device can be vexing, and the vendors don’t make things easy for you to readily compare their features.
In my article posted today on ITworld, I examine several of these products, review what should be in your next RFP if you are in the market to buy an MDM, and what is involved from both the IT manager and the end user perspectives when deploying these tools.
Longing for the days before Wifi was popular
Do you long for the days of yore, when all computers came with a wired Ethernet port and Starbucks was once a coffee shop and not a connectivity destination? Sometimes I do, because life seemed much simpler then. We didn’t have to worry about balancing the radio output on wireless access points, nor worry that a war driver was sitting in the parking lot sucking down bandwidth and trying to penetrate our perimeter. Heck, even the notion of a network perimeter was fairly solid back then.
In an article for HP’s Input Output, I talk about then and now. And I miss those days when we had more wired Ethernet around. It made for some simpler times.
Stop sharing files in public spaces, puh-leeze
I have been on the road a lot this summer, which is always the worst time of year to travel. But one thing I have noticed is that increasingly, many laptop-toting travelers are inadvertently sharing their files when they are on the hotel or airport or coffee shop WiFi.
So here is a short security tip: when you get ready to leave for your next trip, take the two minutes and turn off your file sharing.
Granted, most people aren’t so nosy, or even know how to probe your computer, but why take the chance?
What is amazing is how poorly some hotel and airport networks are constructed, making one big flat space that everyone can see everyone else connected. In some places, there are dozens of computers visible that have sharing turned on.
For those that don’t remember, on the Mac it is System Preferences/ File Sharing. On Windows 7 you can set up different kinds of networks and make it permanent, go to Control Panel/Network and Internet/Network Sharing Center/Advanced sharing settings and then turn off the various options for network discovery, file and print sharing, and public folder sharing for public networks. This way, you can keep sharing on your corporate network and not have to fool with this setting when you travel. On earlier versions of Windows, you will have to turn it off when you travel just like the Mac. You can also go into the wireless network connection property sheet and uncheck the file and printer sharing and Microsoft networking client boxes too.
I know I have been guilty of this myself, and usually am reminded of this when I see the long list of open file servers in my Mac’s Finder window.
There are lots of other steps you can take to make your wireless computing safer, including using a strong firewall (the Win7 built-in one is better than earlier built-in versions) and don’t automatically connect to any available hotspot. And use encryption on your own hotspots at home and in the office, to keep others out.
For more commentary about wireless security issues, check out this piece by Lisa Phifer here from 2008. While old, it is still relevant.
Computerworld: Six annoying router problems
These days, having access to wireless broadband is an absolute necessity for home offices and small businesses. And after more than a decade of innovations, you would think that the standard wireless gateway/router would be a picture-perfect product by now. Alas, no. While many routers offer good features, most still come with flaws that can make life a lot harder, such as confounding setups or limited security.
What follows are six router problems that, quite frankly, I find the most annoying. I looked for possible solutions, and while I didn’t find one router that addressed all my concerns, I did discover features — and routers — that could make things a lot easier. Read my article in Computerworld here.
PC World: Is it time to switch to an all-wireless network?
In a word, yes. If you haven’t looked at your network cabling in a quite awhile, it might be time to consider upgrading to an all-wireless network infrastructure. Why? Because wireless is a very viable option that can connect all your PCs together.
You can read my column in PC World here.
Deploying In-Building Wireless Coverage (Baseline Magazine)
For wireless applications to function properly, they require the right in-building coverage, which involves more than just proper antenna placement and access point design. In this story for Baseline magazine, I look at some of the issues involving in-building coverage.
As wireless becomes more ubiquitous, it enables an entire collection of new applications that can be used to communicate with employees when they are away from their offices, monitor sensors around a building and even transmit video streams.
AT&T USBConnect Mercury laptop broadband adapter card
The idea of going wireless anywhere – not just where you have WiFi – is appealing. And the adapter cards keep getting better. I tried out this 3G card from AT&T on both Windows XP SP2 and SP3 machines – with SP2 you’ll need two reboots to get everything installed. Near the business end of the connector is the SIM card that enables it to work with the AT&T network. The speeds are much better than the 3G connection on my iPhone, with the claims from AT&T of 700-1400 kbps down and 500-1200 kbps uploads about twice what I observed on my 3G iPhone. One oddity – it didn’t like the tracert command in Windows but could do command line FTP transfers just fine. There is also a simplified text messaging application so you can compose texts and send them on the computer keyboard.
If you need on-the-go Web surfing and email, this is a solid product, once you get past the installation. Macs use a different connection manager that comes directly from Sierra Wireless (the makers of the adapter), while Windows uses one that has some added features to help you make free use of AT&T WiFi hot spots. The initial cost of the card is rebated if you get a two-year data plan. If you don’t, the upfront cost is $250. Either way, you still have to pay $60 a month, which includes a 5 GB monthly usage cap before you get charged on additional usage — so if you are going to be transferring a lot of files, this may not be the solution for you.