I caught up with Sam Whitmore recently. Sam and I worked together at PC Week back in the 1980s. We had a ten minute discussion about the presence of analytics in the online newsroom, and their importance and utility to reporters and editors. The conversation came about after we both reviewed a presentation entitled, “Audience insights for the newsroom.” It was given at last year’s Online News Association annual conference by Tess Jeffers, who is the director of Newsroom Data and AI for the Wall Street Journal, and Fernanda Brackenrich, who is the US Audience Engagement editor for Financial Times.
Sam and I spoke about the role that analytics plays to help editors assign stories and shape coverage, comparing my decades of experience freelancing for dozens of publications. The ONA presentation is filled with helpful hints and suggested best practices, all in the name of improving content and increasing influence and reach within Tier 1 newsrooms.
This topic has long been an interest of mine. As I wrote back in 2014, for many years I dutifully kept track of how my blog posts were doing, who was commenting, where backlinks were coming from, and so forth. That post mentions how influence can be found in odd places, and can come from some long tail content that has been around for years, both things that Sam and I touched on during our talk.
This wasn’t the first time I have had a discussion about the relevance of analytics to publishing. Back in 2018, Paul Gillin and I did a podcast interview with Adam Jones with publisher Springer Nature. He spoke about the role of marketing analytics and how he creates stronger calls to action from these insights.
In 2012, I wrote about the work of two Boeing data analysts at a Gartner conference about various efforts using cloud computing and business intelligence projects. One of my insights from that era was to keep your data local and have consistent security controls, advice that is still relevant today (thanks DeepSeek).
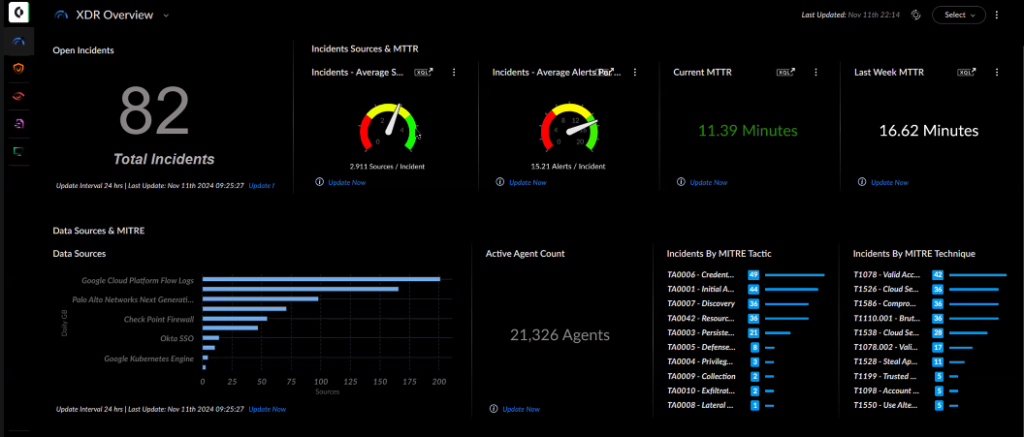
Part of increasing the utility of data analytics is by using appropriate data visualization tools, such as data dashboards. The more patterns you can see graphically, the easier it is to glean something from the parade of numbers on the screen. I wrote about this topic back in 2015, reviewing several municipal applications. During that era, I attended several Tableau user conferences (the company is now a part of Salesforce) where I learned of numerous analytics success stories.
PR people should get to know audience development and data analytics managers such as Jeffers and Brackenrich, because they have their fingers on the pulse of who is reading their pubs and posts.
As all my years writing about tech has taught me, the basics are still important, whether you are dealing with the first IBM PC or the latest AI whizbang model. If you can posit what can build engagement and gather interest, you are already ahead of the game when it comes to pitching a story that can resonate with the right audience.

 The class of products called SOAR, for Security Orchestration, Automation and Response, has undergone a major transformation in the past few years. Features in each of the four words in its description that were once exclusive to SOAR have bled into other tools. For example, responses can be found now in endpoint detection and response tools. Orchestration is now a joint effort with
The class of products called SOAR, for Security Orchestration, Automation and Response, has undergone a major transformation in the past few years. Features in each of the four words in its description that were once exclusive to SOAR have bled into other tools. For example, responses can be found now in endpoint detection and response tools. Orchestration is now a joint effort with