 If you recall the scene in Meet the Parents where the characters played by Robert De Niro and Ben Stiller discuss the “circle of trust,” then today’s blog will resonate with understanding of how your own digital circles of trust are constructed. Recently, Google decided to ban Spanish CA Camerfirma after repeated operational violations. The ban will come into effect with the launch of Chrome version 90, scheduled for release in mid-April. What this means for you, and how digital certificates are used in your daily computing life, are explained in my blog post for Avast here.
If you recall the scene in Meet the Parents where the characters played by Robert De Niro and Ben Stiller discuss the “circle of trust,” then today’s blog will resonate with understanding of how your own digital circles of trust are constructed. Recently, Google decided to ban Spanish CA Camerfirma after repeated operational violations. The ban will come into effect with the launch of Chrome version 90, scheduled for release in mid-April. What this means for you, and how digital certificates are used in your daily computing life, are explained in my blog post for Avast here.
Category Archives: digital home
Haters gonna hate: fighting Holocaust deniers across social media
 A new report from the Anti-Defamation League has reviewed the stated hate speech policies of nine different social media platforms. Unlike other studies, it also tests their responsiveness to user reports of violations of those policies. The ADL is an organization that has been operating for more than 100 years trolling (literally) these waters. They were specifically interested in how social media propagated posts made by Holocaust deniers across their networks. They scored each platform in terms of intentions and how they performed in terms of preventing hate speech on such issues such as:
A new report from the Anti-Defamation League has reviewed the stated hate speech policies of nine different social media platforms. Unlike other studies, it also tests their responsiveness to user reports of violations of those policies. The ADL is an organization that has been operating for more than 100 years trolling (literally) these waters. They were specifically interested in how social media propagated posts made by Holocaust deniers across their networks. They scored each platform in terms of intentions and how they performed in terms of preventing hate speech on such issues such as:
- Did the platform investigate the report and promptly respond (defined as within 24 hours) to the complaint?
- Do users of each platform understand why it has made a certain content decision based on its stated policies?
- Did the platform take any actual action once something was reported?
You can see a part of their report card above. Before I get to the grades given for answering these and other questions, I want to talk about my own personal experience with Holocaust denial. About four years ago, my sister and I went to Poland to see the places where our mom’s family came from. One of our cousins did some genealogy research and found an ancestor who lived in a small town in northeast Poland who was a rabbinical judge back in the 1870s. One of the stops on our trip was to visit Auschwitz, and you can read my thoughts about that day here.
One of the exhibits at the site was about the German engineering firm that designed the mass extermination equipment. For years, the copies of the original drawings used to build this gear were kept from public view by the denier network. But eventually they were sold to someone who flipped from being a denier to someone who realized the legitimacy of these plans, and that’s how we were able to finally see them.
Several years ago I attended a lecture by Jan Grabowski, a history professor from Ottawa. He has done extensive research into Polish Holocaust history, despite the current denier political climate where he and his research associates and colleagues have been threatened and in some cases jailed for their work. Grabowski is affiliated with the Polish Center for Holocaust Research in Warsaw which is attempting to find primary source records to document what happened during those dark times. Add to this a recent survey of millennials that found that 56% of the respondents could not even identify what Auschwitz was about.
From these two personal moments, I realize that we need more evidence-based approaches and to disseminate facts rather than fiction or misdirection. That is where the social networks come into play, because they have become the superhighway of these fictions. Let’s not even glorify them by using the term “alternative facts.”
Let’s return to the report card. Sadly, only Twitter and Twitch acted against the Holocaust denial content reported. No network got any A grades across the ADL’s rubric, to no surprise. Twitch, the gaming social network, scored B’s. Twitter and You Tube got C’s. Facebook and others received grades of D.
Based on its research, the ADL has some recommendations:
- Tech companies must make changes to their products to prioritize users’ safety over engagement and reduce hateful content on their platforms.
- All the platforms need to do a better job on transparency. They should provide users with more information on how they make their decisions regarding content moderation. This is especially urgent, given the recent decisions to terminate several high-profile accounts.
You can read others at the link above. My final point: yes, censoring hate speech — whether it about the Holocaust or whatever — is destructive to our society. Just look at the mob that swarmed across our Capitol earlier this month. The social networks have to decide whether they can step up to the task. And while it bothers me that we have to censor the most dangerous of hate speakers, we do have to recognize their danger.
Avast blog: How to celebrate Data Protection Day
Today is known as “Data Privacy Day” in the US and in other countries around the world, and the theme chosen by the US National Cybersecurity Alliance for this year’s event is about owning your privacy and respecting others. Somehow it seems fitting, given that we have been under lockdown for most of the past year. In my post for Avast’s blog, I talk about some of the ways you can get better at protecting your privacy. But realize that it is a constant struggle, particularly as you can compromise your privacy from so many places in your digital life. The key takeaway to remember is to watch out for your privacy more than once a year.
What’s up with WhatsApp privacy (Avast blog)
Last month, I wrote about the evolution of Instant Messaging interoperability. Since posting that article, the users of WhatsApp have fled. The company (which has been a subsidiary of Facebook for several years now) gave its users an ultimatum: accept new business data sharing terms or delete their accounts. For some of its billion global users, this was not received well, especially since some of your data would be shared across all of Facebook’s other operations and products. The change was indicated through a pop-up message that requires users to agree to the changes before February 8. The aftermath was swift: tens of millions of users signed up for either Signal or Telegram within hours of the news.
If you are interested in getting more of the details and my thoughts about whether to stay with WhatsApp or switch to Telegram or Signal, you should take a gander over on the Avast blog and read my post.
WhatsApp pushed off the change until May, which was probably wise. There was a lot of bad information about what private data is and isn’t collected by the app and how it is shared with the Facebook mothership. For example: while the change deals with how individuals interact with businesses, Facebook has and will continue to share a lot of your contact data amongst its many properties. What this whole debacle indicates though is how little most of us that use these IM apps every day really understand about how they work and what they share. My Avast blog tracks down the particular data elements in a handy hyperlinked reference chart.
The problem is that to be useful your IM app needs to know your social graph. But some apps — such as Signal — don’t have to know much more than your friends’ phone numbers. Others — such as Facebook Messenger — want to burrow themselves into your digital life. I found this out a few years ago when I got my data dump from Facebook, and that was when I deleted the standalone smartphone app. I still use Messenger from my web browser, which is a poor compromise I know.
Speaking of downloading data, I requested my data privacy report from WhatsApp and a few days later got access. There are a lot of details about specific items, such as my last known IP address, the type of phone I use, a profile picture, and various privacy settings, This report doesn’t include any copies of your IM message content, and was designed to meet the EU GDPR requirements. I would recommend you request and download your own report.
 One of the sources that I found doing the research for my blog post was from Consumer Reports that walked me through the process to make WhatsApp more private. You can see the appropriate screen here. Before today, these items were set to “everyone” rather than “my contacts” — there is a third option that turns them off completely. This screen is someplace that I never visited before, despite using WhatsApp for years. It shows you that we have to be vigilant always about our privacy — especially when Facebook is running things — and that there are no simple, single answers.
One of the sources that I found doing the research for my blog post was from Consumer Reports that walked me through the process to make WhatsApp more private. You can see the appropriate screen here. Before today, these items were set to “everyone” rather than “my contacts” — there is a third option that turns them off completely. This screen is someplace that I never visited before, despite using WhatsApp for years. It shows you that we have to be vigilant always about our privacy — especially when Facebook is running things — and that there are no simple, single answers.
Never before have we so many choices when it comes to communicating: IM, PSTN, IP telephony and web conferencing. We have shrunk the globe and made it easier to connect pretty much with anywhere and anyone. But the cost is dear: we have made our data accessible to tech companies to use and abuse as they wish.
Avast blog: Covid tracking apps update
After the Covid-19 outbreak, several groups got going on developing various smartphone tracking apps, as I wrote about last April. Since that post appeared, we have followed up with this news update on their flaws. Given the interest in using so-called “vaccine passports” to account for vaccinations, it is time to review where we have come with the tracking apps. In my latest blog for Avast, I review the progress on these apps, some of the privacy issues that remain, and what the bad guys have been doing to try to leverage Covid-themed cyber attacks.
Avast blog: It’s time to consider getting a Covid-19 vaccine passport for travel
As the number of people getting vaccinated against Covid-19 rises, it’s time to review the ways that people can prove they have been inoculated when they want to cross international borders. These so-called “vaccine passports” have been in development over the past year and are starting to go through various trials and beta tests. The passports would be used by travelers to supplement their actual national passport and other border-crossing documents as they clear customs and immigration barriers. The goal would be to have your vaccination documented in a way that it could be accepted and understood across different languages and national procedures.
In my blog for Avast, I talk about how these passports (such as the CommonPass open source one being developed above) could prove to be a solution for travelers crossing borders, but they also come with their own set of challenges
Where is your phone central office?
 I have written before about my love affair with telephone central offices. This past week, we all now know where Nashville’s CO is located, and we mourn for the people of that city. Nashville is a city that I have been to numerous times, for fun and for business. Little did I realize as I walked among the honky tonk bars and restaurants on Second Street that I was passing by its main CO, which offers a wide range of communication services.
I have written before about my love affair with telephone central offices. This past week, we all now know where Nashville’s CO is located, and we mourn for the people of that city. Nashville is a city that I have been to numerous times, for fun and for business. Little did I realize as I walked among the honky tonk bars and restaurants on Second Street that I was passing by its main CO, which offers a wide range of communication services.
Like the CO that was buried by the collapse of the World Trade Center back in 2001, there was a lot of water damage from the firefighters, and the Nashville repairs were hampered by having to work around the crime scene investigators. But still, within a few days AT&T was able to get various services back up and running, including 911 and airport communications, along with wired and cellular services. The company deployed a series of portable cell towers around the region. The lines that went through this CO connected not just Nashville but areas that were in adjoining states.
This is the conundrum of the CO: in the early days of telephony, they had to be located in densely populated areas, because stringing copper lines from each termination point cost money. To shorten the lines, they had to put them near the people and businesses that they were connecting. This means that you can’t easily protect them with physical barricades a la Fort Knox (or other government buildings). Plus, there are more than 20,000 COs in the US by some estimates. That is a lot of real estate to protect or potentially relocate.
COs are also relatively easy to find, even though many of them are located in nondescript building in major urban areas. My own CO sits like Nashville’s across from a similar collection of restaurants and commercial businesses. There are websites lovingly constructed by other fans of telecom, such as this one or this one that show photos of the actual buildings (although you will have to work a bit to find their street addresses). In my blog post from 2018, I posted pictures of several COs that I have been to, including one on Long Island where I brought my high school networking class on a field trip back in 2001.
Whether or not the bomber was intentionally targeting AT&T’s CO or not, one thing is pretty clear to me: these COs are the weak points in any terror campaign. I don’t have any real solutions to offer up here, just an aching spot in my heart for the men and women that have built them and keep them running.
N.B. This is the last day of a horrible year, a year punctuated with my own personal health story that had nothing to do with Covid. I want to send out a note of thanks to all of you that took the time to send me your support, and hope that you found your own support team to help you along as well. Here is my wish that 2021 will be better for all of us, and that we can support and care for each other to make it so.
Who benefits most from Facebook: the right or the left?
 This piece by Adrienne LaFrance in the Atlantic goes further, saying that Facebook has become the embodiment of the “doomsday machine,” first made popular during the Cold War and the central plot device of Dr. Strangelove, a movie we should rewatch in this new context. “Facebook does not exist to seek truth and report it, or to improve civic health, or to hold the powerful to account,” she says. “It has the power to flip a switch and change what billions of people see online. No single machine should be able to control so many people.”
This piece by Adrienne LaFrance in the Atlantic goes further, saying that Facebook has become the embodiment of the “doomsday machine,” first made popular during the Cold War and the central plot device of Dr. Strangelove, a movie we should rewatch in this new context. “Facebook does not exist to seek truth and report it, or to improve civic health, or to hold the powerful to account,” she says. “It has the power to flip a switch and change what billions of people see online. No single machine should be able to control so many people.”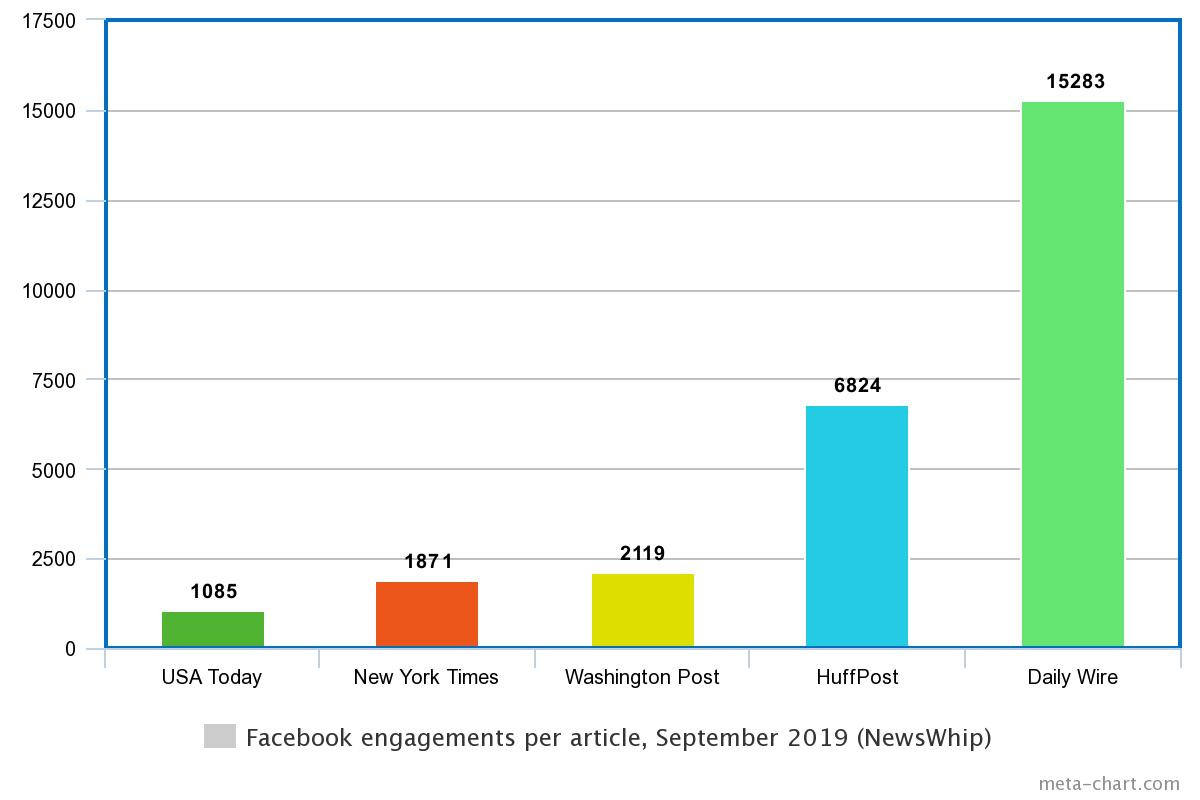
 ut this issue is getting to be old news. Just this past week, Facebook put up this web page, accompanied with full-page newspaper ads claiming that they are on the side of small businesses. They are going after Apple’s attempt to eliminate tracking cookies and make your mobile activities more private. Apple has proposed a pop-up warning when it detects a cross-site cookie, with this mockup. One analysis of the conflict says this illustrates Apple and Facebook’s different approaches to privacy and whether endusers or advertisers will foot the ultimate bill. Regardless, the irony and shameless factor from both companies is too much.
ut this issue is getting to be old news. Just this past week, Facebook put up this web page, accompanied with full-page newspaper ads claiming that they are on the side of small businesses. They are going after Apple’s attempt to eliminate tracking cookies and make your mobile activities more private. Apple has proposed a pop-up warning when it detects a cross-site cookie, with this mockup. One analysis of the conflict says this illustrates Apple and Facebook’s different approaches to privacy and whether endusers or advertisers will foot the ultimate bill. Regardless, the irony and shameless factor from both companies is too much.Securing your IRS online account
 It is hard to believe that it has taken the US IRS all this time to figure out a better authentication mechanism for taxpayers. But starting next month, all taxpayers can apply for an identity protection personal identification number (IP PIN) to block identity thieves from falsely claiming any tax refunds. To give you an idea of the magnitude of this problem, the IRS says several billions of dollars of phony refunds have been prevented through its half-hearted efforts to date. This includes phony refunds that are issued to taxpayers who never filed returns.
It is hard to believe that it has taken the US IRS all this time to figure out a better authentication mechanism for taxpayers. But starting next month, all taxpayers can apply for an identity protection personal identification number (IP PIN) to block identity thieves from falsely claiming any tax refunds. To give you an idea of the magnitude of this problem, the IRS says several billions of dollars of phony refunds have been prevented through its half-hearted efforts to date. This includes phony refunds that are issued to taxpayers who never filed returns.
The IP PIN process used to be for high-risk taxpayers: those who have been victims of refund fraud attempts in the past. Starting next month, we can all join this party (hopefully not the victims group). They explain all of this here, which they call “secure access.”
To participate, you will need a “real” cellular phone number (vs. an IP service like Google Hangouts) and your email address. You will also need a credit card or some other financial instrument (not a debit card) to prove your identity. If you are concerned about giving your phone number to the IRS, you can substitute your postal address and they will send the confirmations that way.
The IP PIN is a six-digit code that changes annually. That is annoying — why not use Google-like authenticator smart phone app — and to make matters more confusing, this differs from the five-digit PIN that is used during the e-filing process for your return. (When I first typed in e-filing, I didn’t use a hyphen and one of the suggestions was effing. That isn’t too far from reality. But I digress.)
Even though the IP PIN effort isn’t happening until next month, you can sign up for your IRS electronic account now. (CORRECTION: The IRS took down the service until January, see the link in my comment.)
This will be a prerequisite for the universal IP PIN process. You’ll notice that particular link isn’t mentioned in the earlier link that explains what secure access is: Dontcha just love our gummint? Anyway, I spent about 20 minutes getting my digital ducks in order for myself and about the same time for my wife’s account. My first credit card for some reason wasn’t accepted, and the site was initially down the time I tried to sign up my wife. I was going to use my Amex card but the IRS doesn’t take that either. Eventually, both of us passed muster and created our accounts It was nice to see that we didn’t owe the IRS any money from past filings.
If this has awakened a desire to be more proactive about protecting your digital identity, Brian Krebs has a bunch of other suggestions that he calls “planting your digital flag.” They are all good ones, although if you are paranoid about your privacy you might want to think about the security tradeoffs you are making.
Book review: Tom Clancy’s Net Force Attack Protocol
 This is the latest in a series of books written by others, in this case by Jerome Preisler. I had high hopes for this book, which is part of a series about a new cybersecurity-enhanced Seal Team type of military commandos. This shows how good an author Clancy is, and how Preisler is just a pale imitation. Like the “Rocky” movie sequels, the book picks up where previous books end, so you really can’t realize your full value if you read it as a standalone volume. And it just ends at some random plot point, without really resolving many of the characters’ situations. Like Clancy, it is filled with jargon, weaponry, mil-speak, and plenty of explosions and gun play. Unlike Clancy, none of this really makes much sense or is essential to moving the plot along, or even mildly interesting. As someone who works in cybersecurity, I thought its treatment of the IT issues were just juvenile and superficial and didn’t draw me into the narrative or characters. Plus, the actual advanced cybersec defenders are less dependent on those macho things that shoot bullets and more on using their brains and computer skills. If you are hungry for more Clancy, pick up one of his old classics like “Red October.” Or if you want to read a series that has much better character and plot development how an actual cybersec team works, check out this series. In either case, you should give this Protocol a pass.
This is the latest in a series of books written by others, in this case by Jerome Preisler. I had high hopes for this book, which is part of a series about a new cybersecurity-enhanced Seal Team type of military commandos. This shows how good an author Clancy is, and how Preisler is just a pale imitation. Like the “Rocky” movie sequels, the book picks up where previous books end, so you really can’t realize your full value if you read it as a standalone volume. And it just ends at some random plot point, without really resolving many of the characters’ situations. Like Clancy, it is filled with jargon, weaponry, mil-speak, and plenty of explosions and gun play. Unlike Clancy, none of this really makes much sense or is essential to moving the plot along, or even mildly interesting. As someone who works in cybersecurity, I thought its treatment of the IT issues were just juvenile and superficial and didn’t draw me into the narrative or characters. Plus, the actual advanced cybersec defenders are less dependent on those macho things that shoot bullets and more on using their brains and computer skills. If you are hungry for more Clancy, pick up one of his old classics like “Red October.” Or if you want to read a series that has much better character and plot development how an actual cybersec team works, check out this series. In either case, you should give this Protocol a pass.