For many IT managers, being cyber aware is a hard thing to pin down. Does this mean that you (really) understand the various potential threat modes that can put your organization at risk? Or that you have some form of regularly scheduled cyber security awareness training happening? Or that you have multiple threat detection and response tools in operation to protect your endpoints? If you have been reading my columns, you know that the best answer is that there is some combination of all three of these elements.
Let’s put this in context, because it is once again time to highlight that October is Cyber Awareness month. Last year I wrote about how security awareness has to be “celebrated” every day, not just in October. Let’s look at some of my recommendations from that blog post and see how far we have come – or not.
My post mentioned four major themes to improve security awareness:
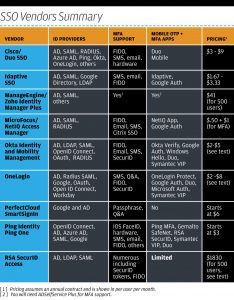
- More comprehensive adoption of multi-factor authentication (MFA) tools and methods,
- Ensuring better backups to thwart ransomware and other attacks,
- Paying more attention to cloud data server configuration, and
- Doing continuous security awareness training.
Sadly, all four of these suggestions are still needed, and many of the past year’s breaches happened because of one or more of them were neglected. There are some bright spots: MFA projects seem to be happening with greater frequency. Single sign-on tools are improving their MFA support, documentation and overall integration making it easier for corporate security developers to add these methods to their own apps. And security awareness training seems to be on the rise as well, with many companies implementing more regular assessments to motivate users to be more careful. This is good, because the bad guys are constantly upping their own game to try to trip us up and force their way into our networks.
But there are also problem areas that have arisen in the past year that bear mention. While ransomware continues to plague many companies, the way that attackers are getting to delivery their ransom attacks is troubling. The news over the past year has shown increased targeting by bad actors. This happens in several ways, including:
- Looking for customers of a single VAR (such as what happened with many local Texas governments),
- Finding those targets who are using a common software supplier (such as what happened with takeovers of disused Github projects), and
- Injecting code into scripts used in other software (such as these Magecart attacks with the ecommerce code used by college campus bookstores).
For these cases, a single exploit caused multiple attacks because of the common software used by their customers. This means that better backups aren’t enough anymore: you also must secure your software supply chain and treat any external software supplier as a potential source of a threat.
This means you need to think about whether your existing security tools can catch such exploits, and if not, what protective measures you can put into place that can. For example, do you have a subresource registry to verify the integrity of your source code? Or do you have a policy to host as many of your third-party scripts on your own servers rather than on any of your suppliers’ servers? Both are worth investigating.
Part of the problem is that attackers are getting more determined: we’ve seen evidence (such as what happened this past year at British Airways) where they have tried multiple entry points and adjusted their methods to find a way inside a targeted network. But a big part of why attackers succeed is because we have very complex technologies in place with multiple failure points. Some of these points are known and protected, but many aren’t. This is why security awareness is a constant battle. Standing still is admitting defeat. So the title of this post isn’t as rhetorical as you might think. Chances are you aren’t as aware as you think you should be, and hopefully I have given you a few ideas to improve.


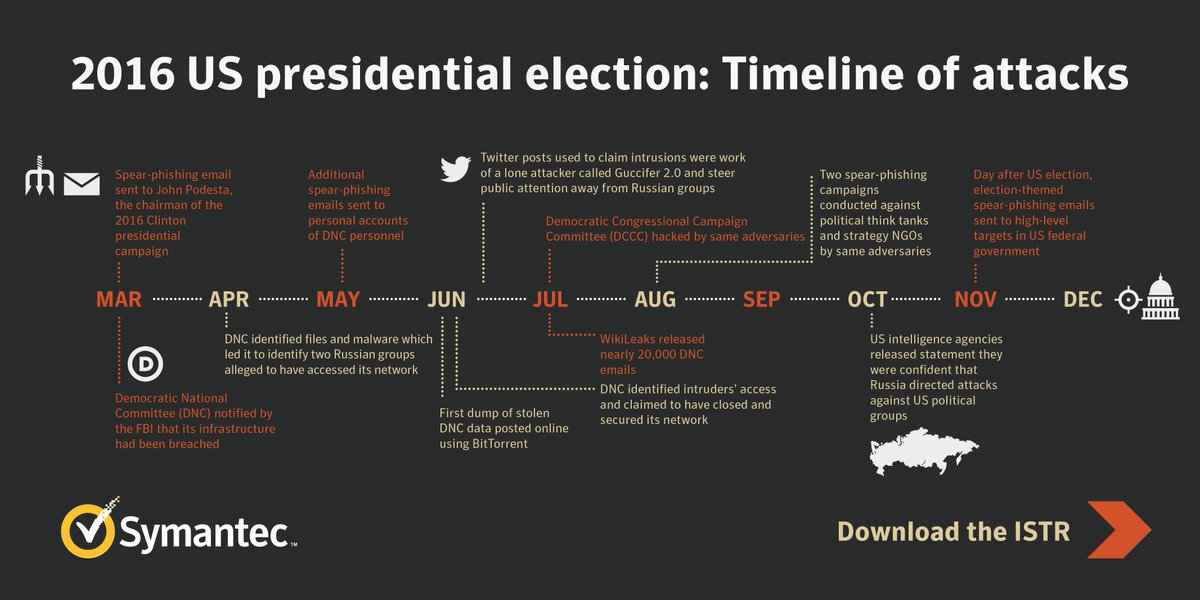 Much of this has already been published, including this timeline
Much of this has already been published, including this timeline