Remember Mirai? This four-year old botnet was the scourge of the internet and used as the launching pad for numerous DDoS attacks. It continues to be the basis for new attacks, and I blog about this for Avast here. There are several mitigation measures you can take, including using a free tool from F-Secure that can check your router for any potential weaknesses. You might also use this to put a more complete program in place to ensure all critical network infrastructure has appropriately complex and unique passwords.
Category Archives: Published work
Network Solutions blog: What is Identity and Access Management and How Does It Protect High-Profile Users?

My latest blog for Network Solutions is about identity and access management. Our email accounts have become our identity, for better and worse. Hackers exploit this dependency by using more clever phishing lures. Until recently, enterprises have employed very complex and sophisticated mechanisms to manage and protect our corporate identities and control access to our files and other network resources. What has changed recently are two programs from Microsoft and Google that are designed to help combat phishing. They are aimed at helping higher-risk users who want enterprise-grade identity and access management security without the added extra cost and effort to maintain it. The two programs are called AccountGuard (Microsoft) and Advanced Security (Google). In my blog post, I explain what these two programs are all about.
Network Solutions blog: Honeypot Network Security, What It Is and How to Use It Defensively
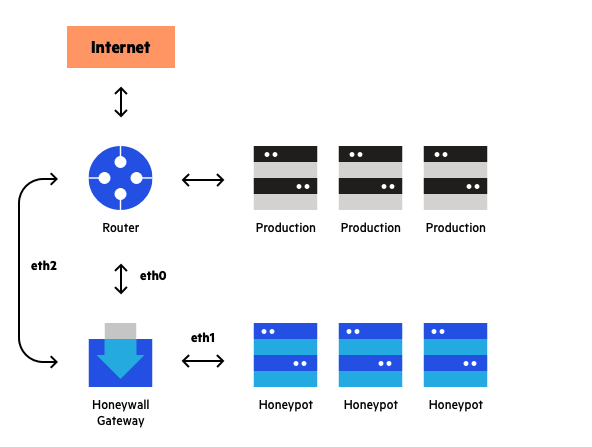 The original idea behind honeypot security was to place a server on some random Internet link and sit back and wait until some hacker happened by. The server’s sole purpose would be to record the break-in attempt — it would not be part of a normal applications infrastructure. Then a researcher would observe what happened to the server and what exploit was being used. A honeypot is essentially bait (passwords, vulnerabilities, fake sensitive data) that’s intentionally made very tempting and accessible. The goal is to deceive and attract a hacker who attempts to gain unauthorized access to your network.
The original idea behind honeypot security was to place a server on some random Internet link and sit back and wait until some hacker happened by. The server’s sole purpose would be to record the break-in attempt — it would not be part of a normal applications infrastructure. Then a researcher would observe what happened to the server and what exploit was being used. A honeypot is essentially bait (passwords, vulnerabilities, fake sensitive data) that’s intentionally made very tempting and accessible. The goal is to deceive and attract a hacker who attempts to gain unauthorized access to your network.
In this blog for Network Solutions, I describe their role in modern network security, compare the features of various commercial and open source products, and provide a series of tips on how to pick the right kind of deception product to fit your business’ needs.
RSA blog: Endpoints are our new security perimeters
Remember when firewalls first became popular? When enterprises began installing firewalls in earnest, they quickly defined our network’s protective perimeter. Over the years, this perimeter has evolved from a hardware focus to one more defined by software, to where Bruce Schneier officially proclaimed their ultimate death a few years ago.
Part of this evolution is the changing nature of the attacks we experience along with the changing nature of our enterprise networks. Back when everyone was working from well-defined offices, we could definitely state that there was a difference between what was considered “outside” and “inside” the corporate network. But then the Internet happened, and we all became connected. Even before the pandemic, there was little difference. With the advent of the cloud, and definitely since the pandemic began, we are all out. That wise infosec sage Jerry Seinfeld once said this in an opening monologue to his TV series in 1989. We no longer worry about “bringing your own device.” We are all working from home, using devices that aren’t necessarily ones that IT has purchased and sharing them with other family members. As my colleague Scott Fulton wrote about this in 2017, “Once the distinctions between inside and outside have been effectively erased, an outside user would be treated exactly the same as one inside the office.” You could argue that he was talking from the opposite perspective, but with the same result.
This has given rise to the concept of zero-trust networks, a topic that I touched upon in my March 2019 post. In that post, I talk about the shades of grey that are now accepted as part of the authentication process: not only is there no distinction between inside and outside the corporate network, but there is nothing that is fully trusted anymore. As I mentioned in that post, the zero-trust concept is really a misnomer: instead, we should strive for a zero-risk model. RSA CTO Dr. Zulfikar Ramzan has long advocated doing this, because it gets IT staffs to examine what is really important: identifying and securing key IT assets and data, as well as that from third parties.
Once consequence of a zero-risk model is that today the new network perimeter really depends on the integrity of our endpoint devices. The endpoint is the first thing that can fall victim to a phishing lure and it is the first place that attackers look for a sign of an unpatched OS or a smartphone that is secretly running malware. Recent surveys show that the pandemic is making it easier for cybercriminals to target mid-level managers, with various lures such as Covid-related ones to more traditional business impersonations.
That doesn’t mean we need to let a thousand firewalls bloom, but it does mean that endpoint detection and response tools have to do a lot more these days than just scan for malware and compromises. Instead, we need a whole army of protective features that is working for us, to prevent our endpoints from being an attractive place for attackers to try to leverage. The vendors in the endpoint space have risen to meet these challenges, and have added features such as:
- Ad hoc queries (to search for new compromises),
- Better security policy enforcement and reporting,
- Automatic discovery of outliers and unmanaged endpoints,
- Detection of lateral network movement (for better early attack notifications),
- Better remediation and deployment tactics (to upgrade large populations of outdated endpoints),
- Better patch management (ditto), and
- Integration into existing protective gear such as event and service management tools.
That is a tall order for any security tool to handle. But as we continue to work from home, we need the appropriate protection. As Pogo once said, “we have met the enemy and he is us.”
RSA blogging
Between 2018-2021, I wrote regularly for various RSA blogs. I was the blogger-in-residence for the annual RSA Archer conference in 2018. I also contributed these (which have since been removed from their website, but here is a record of what I posted from my archives):
- Paying down your technical security debt (1/7/21)
- Security predictions (12/14/20)
- Understanding security chaos engineering (12/9/20)
- Endpoints are the new security perimeter (11/4/20)
- Non-binary security decisions (9/16/20)
- Favorite RSA products of the past (9/1/20)
- Enabling the virtual SOC (08/13/20)
- Making the next digital transition (6/23/20)
- Do you know where your firewalls are located? (5/19/20)
- Think Long-Term: Learning from Today’s Lessons in Business Resiliency (3/25/20)
- Renaissance of the OTP hardware token (3/20/20)
- The tried and true is still relevant (Bruce Schneier book, 2/20)
- Why you need a chief trust officer (12/19)
- Giving thanks and looking forward to 2020 (11/19)
- Are you really cyber aware? (10/19)
- The digital risk challenges of a smart city (9/19)
- Understanding who owns your security infrastructure (8/19)
- Taking hybrid cloud security to the next level (7/19)
- Risk analysis vs. assessment: the key to digital transformation (6/19)
- Managing the security transformation for the truly distributed enterprise (5/19)
- Third-party risk is the soft underbelly of cybersecurity (4/19)
- Understanding the trust landscape (3/19)
- Security predictions for 2019 (12/18)
- Tips to make your Archer deployment successful (11/18)
- Time to practice cybersec awareness every day (October 2018)
- Experts speak out about managing risk (October 2018)
Avast blog: Understanding and preventing Cross-Site Scripting attacks
 You wouldn’t think an attack method that was first found more than 20 years ago would be at the top of anyone’s list of popular current attacks. But that is the case for Cross-Site Scripting (XSS), a method that was first discovered by Microsoft engineers at the turn of the century. Avast’s XSS explainer webpage goes into more detail about the different attack types and some of the more notable attacks and victims down through the years. Top marks were issued by MITRE’s Common Weakness Enumeration group, which also listed 24 other dangerous software weaknesses.
You wouldn’t think an attack method that was first found more than 20 years ago would be at the top of anyone’s list of popular current attacks. But that is the case for Cross-Site Scripting (XSS), a method that was first discovered by Microsoft engineers at the turn of the century. Avast’s XSS explainer webpage goes into more detail about the different attack types and some of the more notable attacks and victims down through the years. Top marks were issued by MITRE’s Common Weakness Enumeration group, which also listed 24 other dangerous software weaknesses.
I describe what all is involved with XSS attacks and some of the more notable ones of recent memory, along with how you can prevent them, in my blog post for Avast here.
Network Solutions blog: Ways to Identify and Prevent Vishing Attacks
 In my latest blog post for Network Solutions, I explain vishing, or voice-based phishing attacks. It is a more modern and sophisticated version of a crank call. Only instead of being placed by bored teenagers, it is a very targeted and dangerous call that can get you to do the caller’s bidding. The vishers are getting more clever at constructing their lures and scams. Spoofing isn’t the only tool these guys abuse. Another is the underpinning of any good social engineering effort: collecting as much data about you as possible, to make their request more personal and more believable. My post has several suggestions to keep in mind the next time you get one of these calls.
In my latest blog post for Network Solutions, I explain vishing, or voice-based phishing attacks. It is a more modern and sophisticated version of a crank call. Only instead of being placed by bored teenagers, it is a very targeted and dangerous call that can get you to do the caller’s bidding. The vishers are getting more clever at constructing their lures and scams. Spoofing isn’t the only tool these guys abuse. Another is the underpinning of any good social engineering effort: collecting as much data about you as possible, to make their request more personal and more believable. My post has several suggestions to keep in mind the next time you get one of these calls.
Network Solutions blog: How to identify and prevent smishing attacks
 By now we are all too familiar with phishing attacks. They have received lots of press coverage and are at the heart of many cyberattacks. But hackers are getting more specialized and have turned towards other variations, one of which goes by the term smishing. This is a combination of social engineering techniques that are sent over SMS texts rather than using the typical emails that traditional phishing lures use. SMS phishing, get it? In Verizon’s 2020 mobile security index, they found that 15% of enterprise users encountered a smishing link in Q3 2019. In my latest post for Network Solutions’ blog, I demonstrate how these kinds of attacks work, how the criminals have upped their game, and what you can do to protect yourself.
By now we are all too familiar with phishing attacks. They have received lots of press coverage and are at the heart of many cyberattacks. But hackers are getting more specialized and have turned towards other variations, one of which goes by the term smishing. This is a combination of social engineering techniques that are sent over SMS texts rather than using the typical emails that traditional phishing lures use. SMS phishing, get it? In Verizon’s 2020 mobile security index, they found that 15% of enterprise users encountered a smishing link in Q3 2019. In my latest post for Network Solutions’ blog, I demonstrate how these kinds of attacks work, how the criminals have upped their game, and what you can do to protect yourself.
Avast blog: One mo’ election update: ransomware
We’re less than a week away from the 2020 U.S. election, and there has been news of a ransomware attack in northern Georgia. The attack hit a network that supports the Hall County government infrastructure and includes election and telephone systems. It was the first time that systems were brought down, although it wasn’t the first time election systems have been targeted by ransomware. Those happened in Louisiana and Washington State, both unsuccessful. In my blog post today for Avast, I go into the details about these attacks and some of the deficient cybersecurity practices also happening in Georgia.
Avast blog: Your data is for sale from election data brokers
By now, many of you know that your online shopping and social media usage patterns can be tracked and recorded. This includes data about your political preferences, which is especially relevant given the approaching elections. Data brokers can use and abuse this information by bundling and selling your data to third parties who are interested in targeting you as a consumer, a buyer, or as a potential voter.
You can read more about this issue in my blog for Avast today and how you can use one of their products, BreachGuard, to help hide your data from brokers and keep improve your privacy posture on social media.