I have been volunteering for the past several months for the American Red Cross and I came across a series of documents, policies, and training about how they use social media that I thought I would share with you. I actually have two very different volunteer jobs with them. First, I work for our local chapter to drive blood to various hospital blood banks. And I work for the national office in DC to help produce a monthly webinar that is attended by hundreds of volunteers and employees involved in their disaster relief efforts. Note that these thoughts are my own, and not necessarily that of the Red Cross.
One thing that I am continually impressed with the Red Cross is how well it partitions and structures the workflows of its volunteers. Even if you volunteer for a relatively low-level position, such as a front desk receptionist, there are manuals that guide what you do and when you do it. This isn’t surprising, given how many of us volunteers there are and how many volunteers are in key leadership roles directing its critical operations. Think about that for a moment: many non-profits give their volunteers the scut work (file these papers that have been lying around here for months). The Red Cross does the opposite, and it is often hard to distinguish between volunteers and staffers when you first meet someone.
A good case in point is my wife, who volunteered in their Santa Monica office years ago after the Katrina floods. Within weeks she was attending staff meetings and eventually she was hired as the chapter’s development director.
But let’s talk about social media, and my first point is the Red Cross’ social media guidelines, which take up all of a single page but have lots of good advice. I thought I would share some of them with you as an example of what you should create for your own business. During my last webinar, Megan Weiler, the senior director of Social Media at their DC HQ gave a presentation on these guidelines and pointed out their six core principles of being a good social citizen:
- Be human, meaning “be your friendly self and use good manners” – too often we tend to post from frustration or to try to right a wrong.
- Be engaging, find others of similar interests and encourage thoughtful discussions.
- Be accurate, make sure news items are verified and give credit for the content you got from someone or somewhere else.
- Be honest, meaning if you mess up, fess up and do so quickly.
- Be considerate, don’t start flame wars. If you have to disagree with someone, do it politely. Also, stay focused on the topic at hand.
- Be safe. Protect your privacy and “be mindful of what you share online.”
These are all great things to keep in mind when you create your own social media posts for your company. What I like about this list is that it gives you the responsibility and boundaries to be successful at delivering messages using social media. Having written and spoken about these topics for more than a decade, I found it a very refreshing take. Too often corporations are heavy-handed about directing their employees’ use of social media. That heavy hand results in social media misfires or sock puppetry that doesn’t serve anyone well. (Take as a case in point of the Twitter account of a certain former White House staffer earlier this month as an example.)
Some corporations were early advocates of social media like Dell, who subsequently put together a central social media command center at its corporate offices outside of Austin. That may work well for them (I wrote this analysis of Dell’s effort back in 2011) and indeed the Red Cross has its own digital operations nerve center to help with its disaster relief efforts. But this is just one aspect of what the Red Cross does and managing their gigantic global volunteer staff at the Red Cross has some other circumstances and wider implications. They actually understand that social media engagement is a critical component of their operational DNA and sharing a volunteer’s personal story is part of their mission.
You might wonder why I am driving blood around town. My reason was simple: it was an extension of the many years where I donated blood and I liked being more involved and getting to understand their infrastructure to bring blood units to those who need them. It isn’t intellectually challenging – other than keeping track of where in each hospital the blood labs are located – but it deepens my involvement. (Did you notice how I just shared my personal story here?) BTW, for those of you that donate blood, thanks for helping out!
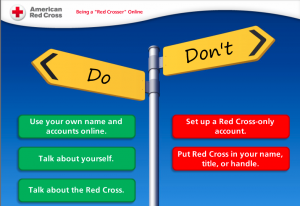
Finally, the Red Cross has a half-hour online training course on social media basics that are only available to volunteers. The class walks you through what social listening is all about and how to get you more engaged in participating in social media as a Red Crosser. The class also makes a distinction between a volunteer implying they are running an official Red Cross social media account, versus their saying that they only represent themselves. That is an important distinction.
 The class goes into further details:
The class goes into further details:
- If you post anything about the Red Cross, make sure you disclose your role and use your real name. Disclose any vested self-interest and write about your own expertise.
- Respect your dignity, privacy and confidences. Be sensitive to the community you are serving, be cautious about sharing information before it is vetted.
- “Remember if you are online, you are on the record.” This is probably the most important aspect of social media that many of us tend to forget.
- Understand that your personal social media accounts are your identity. You should certainly include your corporate affiliation in your online bios but shouldn’t construct your Twitter handle around them. For example, create a handle such as @dstrom, rather than @redCrossStrom. Maintain the balance of what is personal and what is professional. Some companies want you to operate their social media accounts – while that could work in certain circumstances, the Red Cross wants you to be you.



 This is the
This is the 
 We’re joined by
We’re joined by 