Let’s talk about what makes for a successful corporate blog and how you can assemble one of your own. Blogs are an essential element of any corporate marketing strategy, and should be the linchpin of creating an integrated digital marketing campaign that includes email newsletters, social media posts, and other kinds of content. But if you don’t have a strong blog, you will have a difficult time executing any solid marketing campaign.
I have written about corporate blogging for more than 13 years, including this story that ran in Computerworld, and contributed to dozens of different corporate blogs (in addition to running some websites that could be considered blogs if they were created in the modern era). Jeremiah Owyang once said that you shouldn’t accept blogging advice from people that are not bloggers. Given that he has blogged for as long (if not longer) than I have, he is worth paying attention to. I am writing about this again thanks to being inspired by a recent article about Autodesk and its 200-some corporate blogs.
 Autodesk is the company behind AutoCAD and some 170 other products that are based on that industry segment. When you first see how many blogs they have, you think: that can’t possibly be the right strategy for them. But the more you look into what they are doing, the more you understand that this is actually brilliant. These different blogs (some of which you can see in the screen capture here) show something more than just quantity. For example, each Autodesk product and blog has its own dedicated marketing team, so it’s up to each to decide how to structure its operation and tell it’s own story. So as you are examining what Autodesk is doing, here are a few pointers.
Autodesk is the company behind AutoCAD and some 170 other products that are based on that industry segment. When you first see how many blogs they have, you think: that can’t possibly be the right strategy for them. But the more you look into what they are doing, the more you understand that this is actually brilliant. These different blogs (some of which you can see in the screen capture here) show something more than just quantity. For example, each Autodesk product and blog has its own dedicated marketing team, so it’s up to each to decide how to structure its operation and tell it’s own story. So as you are examining what Autodesk is doing, here are a few pointers.
First is understanding the key elements in assembling your team that will staff and run a blog. It is more akin to running a publication (something that I have done numerous times over my career in both print and online), but you may not have editorial and production people in-house. That is why it could make sense to outsource part of these back or front office functions of the blog to operations such as Skyword or Contently. While you pay a premium for these services, they can deliver benefits if you don’t have the time, skills or staff to handle these functions. Another part of successful blogging is creating an editorial calendar and planning what you will cover in the next quarter (or longer if you can), posting regularly and selecting the right topics. This makes it easier to assign posts and organize your campaigns.
Next, you need to understand your audience focus and define what the overall purpose of the blog or blogs will be, as well as adjusting to the appropriate level of knowledge for a particular readership. This is something that you want to do up front, before you start creating any posts.
It is also important to take the long view about your blog or blogs; on the Internet, content is eternal and many corporate marketers often make the mistake of having a blog stand up for just a particular campaign. I often get inquiries from something that I posted ten years ago. Many of the blogs and pubs that I have written for have taken down their content. Newsflash: storage and domain services are cheap these days.
Part of any successful blog is also figuring out what your metrics for success are, and that should involve more than just counting simple page views. While we all watch that particular statistic, it doesn’t tell the entire story, such as how engaged our readers are and how many of them convert to trial product versions or refer others who become customers. Figure out how you can track these things effectively.
Finally, make sure you pay your external writers quickly and without a lot of paperwork, otherwise they will migrate elsewhere. (That is where the outsourced back office providers can help.) I know this sounds somewhat self-serving, but I have seen many fine pubs lose talented writers who get frustrated when payments stretch out for months.
If you haven’t had enough suggestions, or if you want to send these suggestions to someone who is a more auditory learner, you can listen to a 20 minute podcast that Paul Gillin and I put together for our FIR B2B episode this week here.
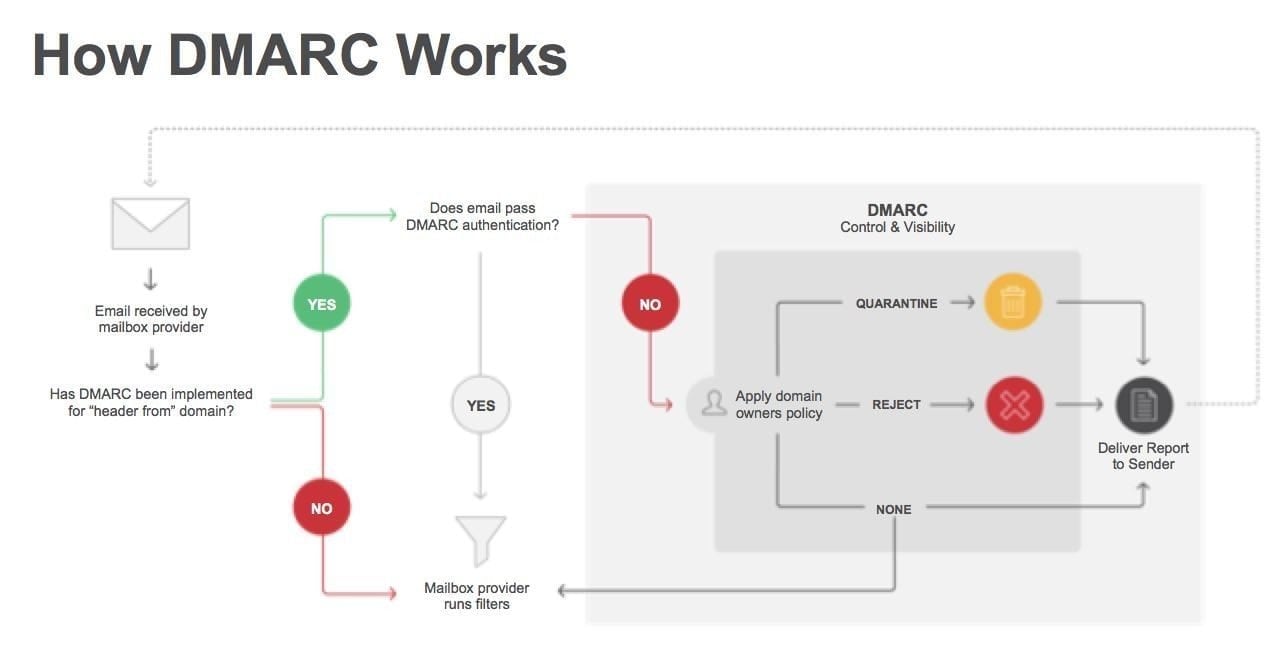 Phishing and email spam are the biggest opportunities for hackers to enter the network. If a single user clicks on some malicious email attachment, it can compromise an entire enterprise with ransomware, cryptojacking scripts, data leakages, or privilege escalation exploits. Despite making some progress, a trio of email security protocols has seen a rocky road of deployment in the past year. Going by their acronyms SPF, DKIM and DMARC, the three are difficult to configure and require careful study to understand how they inter-relate and complement each other with their protective features. The effort, however, is worth the investment in learning how to use them.
Phishing and email spam are the biggest opportunities for hackers to enter the network. If a single user clicks on some malicious email attachment, it can compromise an entire enterprise with ransomware, cryptojacking scripts, data leakages, or privilege escalation exploits. Despite making some progress, a trio of email security protocols has seen a rocky road of deployment in the past year. Going by their acronyms SPF, DKIM and DMARC, the three are difficult to configure and require careful study to understand how they inter-relate and complement each other with their protective features. The effort, however, is worth the investment in learning how to use them. Organizations are becoming increasingly digital in their operations, products and services offerings, as well as with their business methods. This means they are introducing more technology into their environment. At the same time, they have shrunk their IT shops – in particular, their infosec teams – and have less visibility into their environment and operations. While they are trying to do more with fewer staff, they are also falling behind in terms of tracking potential security alerts and understanding how attackers enter their networks. Unfortunately, threats are more complex as criminals use a variety of paths such as web, email, mobile, cloud, and native Windows exploits to insert malware and steal a company’s data and funds.
Organizations are becoming increasingly digital in their operations, products and services offerings, as well as with their business methods. This means they are introducing more technology into their environment. At the same time, they have shrunk their IT shops – in particular, their infosec teams – and have less visibility into their environment and operations. While they are trying to do more with fewer staff, they are also falling behind in terms of tracking potential security alerts and understanding how attackers enter their networks. Unfortunately, threats are more complex as criminals use a variety of paths such as web, email, mobile, cloud, and native Windows exploits to insert malware and steal a company’s data and funds. The world has changed significantly in the past two years, and so have the rules around assessing cyber security risk. A combination of greater digital business penetration, a wider array of risks, and bigger consequences of cyber threats have made the world of risk management both more complex and more important than ever. Sadly, word hasn’t yet gotten out that risk management is an essential part of today’s business operations. According to this
The world has changed significantly in the past two years, and so have the rules around assessing cyber security risk. A combination of greater digital business penetration, a wider array of risks, and bigger consequences of cyber threats have made the world of risk management both more complex and more important than ever. Sadly, word hasn’t yet gotten out that risk management is an essential part of today’s business operations. According to this 
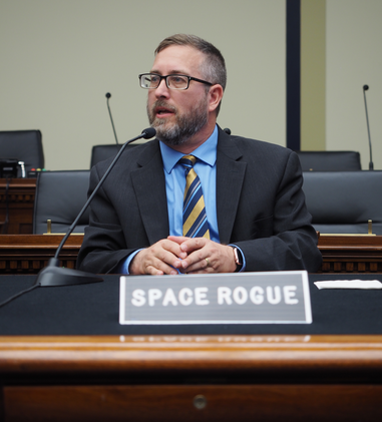 Cris Thomas, who also goes by the pseudonym
Cris Thomas, who also goes by the pseudonym  There are conflicting reports over whether or not ransomware attacks are growing. Many organizations state (quite convincingly) that it’s the most popular malware form and that ransom-related attacks have been increasing at a rapid rate over the past year. However, other reports offer a more nuanced point of view.While the raw number of ransom-based attacks is increasing, the proportion of ransom-related attacks is dropping over the last part of 2017. Many businesses are not paying out the ransoms, motivating criminals to try other malware methods.
There are conflicting reports over whether or not ransomware attacks are growing. Many organizations state (quite convincingly) that it’s the most popular malware form and that ransom-related attacks have been increasing at a rapid rate over the past year. However, other reports offer a more nuanced point of view.While the raw number of ransom-based attacks is increasing, the proportion of ransom-related attacks is dropping over the last part of 2017. Many businesses are not paying out the ransoms, motivating criminals to try other malware methods.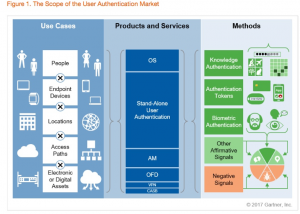
 Autodesk is the company behind AutoCAD and some 170 other products that are based on that industry segment. When you first see how many blogs they have, you think: that can’t possibly be the right strategy for them. But the more you look into what they are doing, the more you understand that this is actually brilliant. These different blogs (some of which you can see in the screen capture here) show something more than just quantity. For example, each Autodesk product and blog has its own dedicated marketing team, so it’s up to each to decide how to structure its operation and tell it’s own story. So as you are examining what Autodesk is doing, here are a few pointers.
Autodesk is the company behind AutoCAD and some 170 other products that are based on that industry segment. When you first see how many blogs they have, you think: that can’t possibly be the right strategy for them. But the more you look into what they are doing, the more you understand that this is actually brilliant. These different blogs (some of which you can see in the screen capture here) show something more than just quantity. For example, each Autodesk product and blog has its own dedicated marketing team, so it’s up to each to decide how to structure its operation and tell it’s own story. So as you are examining what Autodesk is doing, here are a few pointers. In an article that I wrote last week for CSOonline, I d
In an article that I wrote last week for CSOonline, I d