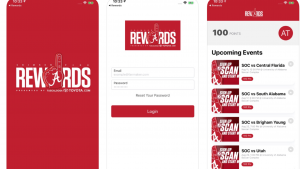
 I gave a talk at our local Venture Cafe about this topic and thought I would summarize some of my suggestions in a blog post here. We all know that our devices leak all sorts of personal data: the locations and movements of our phones, the contents of our emails and texts, the people with whom we communicate, and even the smart devices in our homes are all chatty Cathys. There have been numerous articles that describe these communications, including how an app for the University of Alabama’s football team tracks students who agree to divulge their game attendance in return to obtain rewards points for college merch (see the screenshot here). Another NY Times story analyzed the tracking resources when a reporter visited dozens of different websites. The trackers from these sites were able to determine where the reporter lived and worked and could collect all sorts of other personal information, including finding out when women who were using phone apps to track their monthly periods were having sex.
I gave a talk at our local Venture Cafe about this topic and thought I would summarize some of my suggestions in a blog post here. We all know that our devices leak all sorts of personal data: the locations and movements of our phones, the contents of our emails and texts, the people with whom we communicate, and even the smart devices in our homes are all chatty Cathys. There have been numerous articles that describe these communications, including how an app for the University of Alabama’s football team tracks students who agree to divulge their game attendance in return to obtain rewards points for college merch (see the screenshot here). Another NY Times story analyzed the tracking resources when a reporter visited dozens of different websites. The trackers from these sites were able to determine where the reporter lived and worked and could collect all sorts of other personal information, including finding out when women who were using phone apps to track their monthly periods were having sex.
Most of us have some basic understanding about how web tracking cookies work: this technology is decades old. But that era seems so quaint now and the problem is that our phones are powerful computers that can track all sorts of other stuff that can be more invasive. It also doesn’t help that our phones are usually with us at all times. Reading the two NYT pieces should make anyone more careful about what information you should give up to the digital overlords that control our apps. In my talk I present a few tools to fight back and provide more privacy protection. They include:
- Monitor your Wifi usage and then choose the right VPN that offers the best protection. Open Wifi networks can collect everything that you are doing online: you should find and use the right VPN to at least encrypt these conversations. The problem is many VPNs are owned by Chinese vendors or that collect other information about you. Two studies are worth reviewing: one by Privacy Australia which has a nice analysis of which are faster performers and one by Top10VPN which goes into details about who owns each vendor. I use ProtonVPN on both my phone and laptop.
- Choose passwords carefully and use a password manager. I have made this recommendation before, do take it seriously if you still are a hold out. Reusing passwords is the single biggest mistake you can make towards compromising your privacy. I use LastPass on all my devices.
- Change your DNS settings to provide additional protection. There are now numerous alternative DNS providers that can help encrypt and hide your web traffic, as well as provide for faster connections. Cloudflare has two tools, including its 1.1.1.1 DNS service and its Warp phone VPN service. Both are free.
In my talk I also have several main strategies towards better privacy protection. These include:
- Eliminate very personal data on social media, such as your real birthday and other identifying information. Be careful about future posts and whom you tag on your social media accounts too.
- Delete the Facebook Messenger phone app: it scraps your entire contact list and uploads it to Facebook. Don’t use social media identities as login proxies if you can avoid them.
- Audit your phones regularly and eliminate unneeded apps. Know which ones are leaking data and avoid them as well. The app Mighty Signal will report on what is leaked.
- Set up your phone for optimum privacy protection. This involves several steps, including updating to the latest iOS and Android OS versions and enable their latest privacy features, such as stripping photo location metadata and blocking unknown callers. A good place to start is to use the JumboPrivacy App to further restrict your data leakage too: it will recommend the most private settings for you, given how complex the average phone app is these days and how hard it is to figure out how to configure each app appropriately.
- If you are truly concerned, move to a different browser and search tool, such as Brave and DuckDuckGo that offer more privacy protection. Yes you will give up some functionality for this protection, so you have to weigh the tradeoffs of utility versus protection.
This seems like a lot of work, and I won’t deny that. Take things one step at a time, and change one habit and understand its consequences (including loss of functionality and convenience) before moving on to making other changes. Too often folks can easily get overwhelmed and then retreat to old habits, nullifying these improvements. When you have a choice, pick technologies that are easier to manage and implement.
Do let me know what your own experiences have been along this journey too by posting a comment here if you’d like.
Good list. One note: the “app Mighty Signal” link goes nowhere, and MightySignal.com appears to be yet another company in the icky marketing business.
Remember the 1990’s, when security was mostly about making sure nobody but you could run programs on your computer? Now we allow every web site owner to run JavaScript on our personal computer. But .. most sites are useful without JavaScript enabled. And when you find a site which is not useful without JavaScript, you will find that you only need to enable some of the JavaScript. Most of it is for the marketing folks, and a bit of it is for the user’s needs. It is a bother, but you can use umatrix to select which JavaScript you will permit.
I’ve been using ExpressVPN and 1Password for my laptop and phone. I think a VPN and password manager combined offers a more holistic approach to securing your network. I have 100s of different passwords and they’re all robust.