When someone tries to steal money from your bank or credit card accounts, these days it is a lot harder, thanks to a number of technologies. I recently personally had this situation. Someone tried to use my credit card on the other side of Missouri on a Sunday afternoon. Within moments, I got alerts from my bank, along with a toll-free number to call to verify the transactions. In the heat of the moment, I dialed the number and started talking to my bank’s customer service representatives. Then it hit me: what if I were being phished? I told the person that I was going to call them back, using the number on the back of my card. Once I did, I found out I was talking to the right people after all, but still you can’t be too careful.
 This heat-of-the-moment reaction is what the criminals count on, and how they prey on your heightened emotional state. In my case, I was well into my first call before I started thinking more carefully about the situation, so I could understand how phishing attacks can often work, even for experienced people.
This heat-of-the-moment reaction is what the criminals count on, and how they prey on your heightened emotional state. In my case, I was well into my first call before I started thinking more carefully about the situation, so I could understand how phishing attacks can often work, even for experienced people.
To help cut down on these sorts of exploits, banks use a variety of risk-based or adaptive authentication technologies that monitor your transactions constantly, to try to figure out if it really is you doing them or someone else. In my case, the pattern of life didn’t fit, even though it was a transaction taking place only a few hundred miles away from where I lived. Those of you who travel internationally probably have come across this situation: if you forget to tell your bank you are traveling, your first purchase in a foreign country may be declined until you call them and authorize it. But now the granularity of what can be caught is much finer, which was good news for me.
These technologies can take several forms: some of them are part of identity management tools or multi-factor authentication tools, others come as part of regular features of cloud access security brokers. They aren’t inexpensive, and they take time to implement properly. In a story I wrote last month for CSOonline, I discuss what IT managers need to know to make the right purchasing decision.
In that article, I also talk about these tools and how they have matured over the past few years. As we move more of our online activity to mobiles and social networks, hackers are finding ways at leveraging our identity in new and sneaky ways. One-time passwords that are being sent to our phones can be more readily intercepted, using the knowledge that we broadcast on our social media. And to make matters worse, attackers are also getting better at conducting blended attacks that can cut across a website, a mobile phone app, voice phone calls, and legacy on-premises applications.
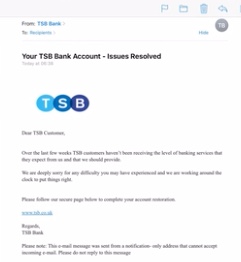
Of course, all the tech in the world doesn’t help if your bank can’t respond quickly when you uncover some fraudulent activity. Criminals specifically targeted a UK bank that was having issues with switching over its computer systems last month, knowing that customers would have a hard time getting through to its customer support call centers. The linked article documents how one customer waited on hold for more than four hours, watching while criminals took thousands of pounds out of his account. Other victims were robbed of five and six-figure sums after falling for phishing messages that asked them to input their login credentials.
Steve Ragan in a screencast below shows you the phishing techniques that were used in this particular situation.
The moral of the story: don’t panic when you get a potentially dire fraud alert message. Take a breath, take time to think it through. And call your bank when in doubt.
Good post. What continues to bug me is that banks don’t ask “Did you call this number from the back of your card?” Those of us who did will say “Of course”, but we aren’t the ones to worry about. I’ve gotten calls from banks asking me about transactions; when I said “I will call you back”, they said “Fine, of course”. But they SHOULD have started the call with “This is TBTF Bank, calling about a questionable transaction on your Visa card. To ensure that this is a legitimate conversation, please call us back at the number on the back of your card.”