![Space Rogue: How the Hackers Known As L0pht Changed the World by [Cris Thomas]](https://m.media-amazon.com/images/I/41OEoTKDqTL.jpg) The hacker Cris Thomas, known by his hacker handle Space Rogue, has a new book out that chronicles his rise into infosec security. I have interviewed him when I was writing for IBM’s Security Intelligence blog about his exploits. IBM’s X-Force has been his employer for many years now where he works for numerous corporate clients, plying the tools and techniques he refined when he was one of the founding members of the hacking collective L0pht.
The hacker Cris Thomas, known by his hacker handle Space Rogue, has a new book out that chronicles his rise into infosec security. I have interviewed him when I was writing for IBM’s Security Intelligence blog about his exploits. IBM’s X-Force has been his employer for many years now where he works for numerous corporate clients, plying the tools and techniques he refined when he was one of the founding members of the hacking collective L0pht.
My story covered his return visit to testify to Congress in 2018. Thomas and his colleagues originally testified there back in 1998. The book’s cover art shows this pivotal moment, along with the hacker handles shown as nameplates. The story of how this meeting came to pass is one of the book’s more interesting chapters, and the transcript of their testimony is included in an appendix too.
I also wrote this post about another member of L0pht named Mudge, during his time as a security consultant for Twitter. L0pht is infamous for developing a series of hacking tools, such as Windows NT password crackers (which Thomas goes into enormous detail about the evolution and enhancement of this tool) and a website called Hacker News Network. Thomas describes those formative years with plenty of wit and charm in his new book, which also serves as a reminder of how computer and network security has evolved — or not as the case may be made.
That cracking tool carried L0pht over the course of some twenty plus years. It began as “a small little piece of proof of concept code, hurriedly produced within a few weeks, and went from an exercise to prove a point, security weaknesses in a major operating system, to shareware, to a commercial success,” he writes.
One of his stories is about how L0pht had its first major penetration test of the Cambridge Technology Partners network. The company would go on to eventually purchase Novell and numerous other tech firms. The hackers managed to get all sorts of access to the CTP network, including being able to listen to voicemails about the proposed merger. The two companies were considering the acquisition of L0pht but couldn’t come to terms, and the hackers had left a backdoor in the CTP network that was never used but left on because by then their testing agreement had expired. Fun times.
The early days of L0pht were wild by today’s standards: the members would often prowl the streets of Boston and dumpster dive in search of used computer parts. They would then clean them up and sell them at the monthly MIT electronics flea market. Dead hard drives were one of their specialties — “guaranteed to be dead or your money back if you could get them working.” None of their customers took them up on this offer, however.
One point about those early hacking days — Thomas writes that the “naïveté of hackers in the late ’90s and early 2000s didn’t last long. Hackers no longer explore networks and computer systems from their parents’ basements (if they ever did); now it is often about purposeful destruction at the bequest of government agencies.”
He recounts the story of when L0pht members brought federal CyberCzar Richard Clarke to their offices in the 1990s. Clarke was sufficiently impressed and told Thomas, “we have always assumed that for a group or organization to develop the capabilities that you just showed us would take the resources only available to a state-sponsored actor. We are going to have to rethink all of our threat models.” Exactly.
There are other chapters about the purchase of L0pht by @stake and Thomas’ eventual firing from the company, then taking eight years to get a college degree at age 40, along with the temporary rebirth of the Hacker News Network and going to work for Tenable and now at IBM.
Thomas ends his book with some words of wisdom. “Hackers are not the bad guys. Most of the great inventors of our time, such as Alexander Graham Bell, Mildred Kenner, and Nichola Tesla, could easily be considered hackers. Criminal gangs who are running ransomware campaigns or are stealing credit cards are just that, criminals. They just happen to use a computer instead of a crowbar. They are not hackers, not to me anyway. L0pht’s message of bringing security issues to light and getting them fixed still echoes throughout the industry and is more important today than ever.” If you are at all interested in reading about the early days of the infosec industry, I highly recommend this book.

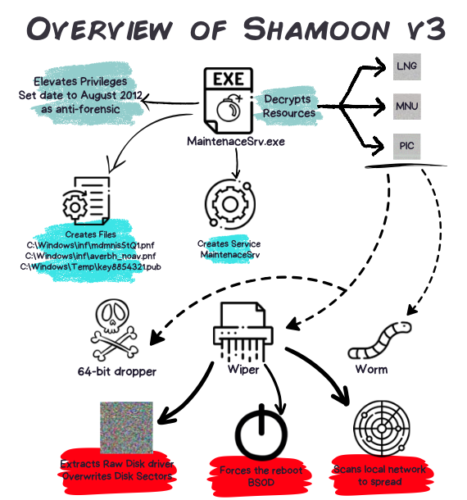 mapping the attack to the diamond model (focusing on adversaries, infrastructure, capabilities, and victims) and a summary of the MITRE ATT&CK tactics. That is a lot of specific information that is presented in a easily readable manner. I have been writing about cybersecurity for many years and haven’t seen such a cogent collection in one place of these more infamous attacks.
mapping the attack to the diamond model (focusing on adversaries, infrastructure, capabilities, and victims) and a summary of the MITRE ATT&CK tactics. That is a lot of specific information that is presented in a easily readable manner. I have been writing about cybersecurity for many years and haven’t seen such a cogent collection in one place of these more infamous attacks. I have known Bruce Schneier for many years, and met him most recently just after he gave one of the keynotes at this year’s RSA show. The keynote extends his thoughts in his
I have known Bruce Schneier for many years, and met him most recently just after he gave one of the keynotes at this year’s RSA show. The keynote extends his thoughts in his  I liked the conceit about this murder mystery novel by Hannah Mary McKinnon entitled
I liked the conceit about this murder mystery novel by Hannah Mary McKinnon entitled ![Stalked by Revenge (Zane Clearwater Mystery Book 3) by [Lynn Lipinski]](https://m.media-amazon.com/images/I/41tkpMWe6jL.jpg) This is the third book in a series of mystery novels featuring Zane Clearwater, a character who has had a shady past. It can be read independently of the others and there is a fourth is in the works. The story centers on Clearwater’s family, including a gun-packing grandmother and a private detective who comes to the aid of the family to stop a revengeful assailant who starts out in prison at the story’s beginning. Lipinski’s descriptive prose is first-rate, and the various characters are well drawn, with some very realistic challenges in their lives. By the end of the book you will feel that you know them and have a lot of empathy for their circumstances. Fans of mystery novels will enjoy this book, and I highly recommend it.
This is the third book in a series of mystery novels featuring Zane Clearwater, a character who has had a shady past. It can be read independently of the others and there is a fourth is in the works. The story centers on Clearwater’s family, including a gun-packing grandmother and a private detective who comes to the aid of the family to stop a revengeful assailant who starts out in prison at the story’s beginning. Lipinski’s descriptive prose is first-rate, and the various characters are well drawn, with some very realistic challenges in their lives. By the end of the book you will feel that you know them and have a lot of empathy for their circumstances. Fans of mystery novels will enjoy this book, and I highly recommend it.![A Likely Story: A Novel by [Leigh McMullan Abramson]](https://m.media-amazon.com/images/I/41GrD0EcOLL.jpg) I really
I really 
![Space Rogue: How the Hackers Known As L0pht Changed the World by [Cris Thomas]](https://m.media-amazon.com/images/I/41OEoTKDqTL.jpg) The hacker Cris Thomas, known by his hacker handle Space Rogue, has
The hacker Cris Thomas, known by his hacker handle Space Rogue, has  My stepson died last year of throat cancer, brought on by years of alcohol and tobacco abuse. I say this because I thought this was going to be a hard book to read — part memoir, part 12-step navigational handbook, part Big Thoughts. That doesn’t sound like I liked the book, but I did, and thought Levy spoke to me about my stepson and his various demons that he fought and lost. She fought and has won, but it was a hard fight, filled with many missteps and disastrous mistakes.
My stepson died last year of throat cancer, brought on by years of alcohol and tobacco abuse. I say this because I thought this was going to be a hard book to read — part memoir, part 12-step navigational handbook, part Big Thoughts. That doesn’t sound like I liked the book, but I did, and thought Levy spoke to me about my stepson and his various demons that he fought and lost. She fought and has won, but it was a hard fight, filled with many missteps and disastrous mistakes.![Sam: A Novel by [Allegra Goodman]](https://m.media-amazon.com/images/W/WEBP_402378-T2/images/I/41XMhRgw6qL.jpg)