First off, mea culpa for sending out that test message earlier this month. As you might have guessed, I have moved everyone to a new listserv (still using Mailman after all these years) at Pair.com, and things seem to be working. LMK if you want to be removed or have your address updated or have issues with the mailings.
Last week was not a quiet week in Lake Wobegon, where all of my sources are above average. I flew for the first time domestically on business, and (unlike the fictional town) the flights and airports were crowded, but everyone was masked up and behaving, thankfully. The trip was to visit the Cyber Shield exercises held at the Utah National Guard base outside of Salt Lake City. I was staying on the base across the street from the monster NSA data center that you can see in the background.
The Guard story is posted here on Avast’s blog. I write about how the Guard is using live cyber ranges to train its cyber soldiers and the very realistic scenarios it is using. The dedication of the 800-some participants during this two-week event was amazing to see first-hand, and I appreciated all the time the Guard took to explain what they were doing and give me some of their stories of how they got involved with both the Guard and how it related to their careers in cybersecurity.
I also wrote another post for Avast about the Pegasus Project that was the work of security researchers at The Citizen Lab in Toronto, the Security Lab of Amnesty International in Berlin, and the Forbidden Stories project in Paris. Pegasus is a surveillance tool sold by the Israeli private firm NSO Group. It can be deployed on both Apple and Android phones with incredible stealth, to the point that targets don’t even know it is there.
The three groups examined phones from 67 people and found 34 iPhones and three Androids had contained traces of Pegasus – about a third of these had evidence that Pegasus had successfully compromised each phone. What was interesting was two items: First, one of the hacked iPhones was running the most current version of iOS. Second, many of the targets show a very tight correlation between the timestamps of the files deposited by Pegasus and particular events that link to the monitoring of the victim. Someone was very interested in these people, which ranged from politicians to journalists, someone who was a client of NSO and could target their tool to these people.
Several years ago, one of my contacts showed me the power of Pegasus on a test phone at my office and it was scary how easily the spyware could collect just about anything on the phone: texts, pictures, IP addresses, phone contacts, and so forth. If you want to read more about this project, several media outlets have written stories about it and are linked in my Avast blog.
Since I am in self-promotions mode, you might also want to check out some of my other work that I have written recently:
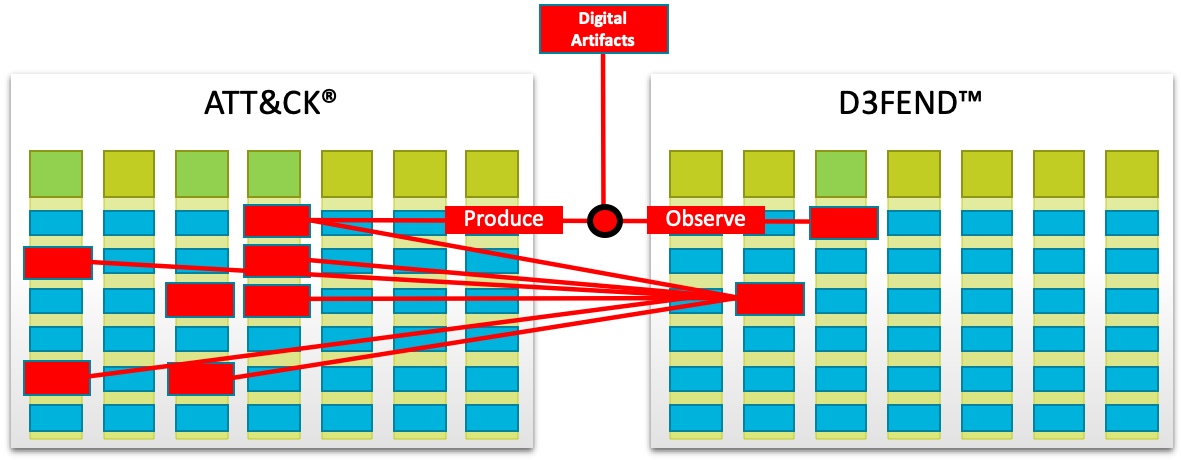
- A story for CSOonline about a new defensive knowledge graph done by Mitre for the NSA called D3FEND. The project will help IT managers find functional overlap in their security tools and help guide new purchases as well as make better defensive decisions.
- A podcast about a new report by Forrester that Paul Gillin and I recorded about the changing landscape of B2B discussion groups. The 14 minute conversation is how the shift from LinkedIn to Facebook groups has evolved and why IT vendors and channel partners should pay attention to the other social network outlets.