 The biggest cyber threat isn’t sitting on your desk: it is in your pocket or purse. I am talking of course about your smartphone. Our phones have become the prime hacking target, due to a combination of circumstances, some under our control, and some not.
The biggest cyber threat isn’t sitting on your desk: it is in your pocket or purse. I am talking of course about your smartphone. Our phones have become the prime hacking target, due to a combination of circumstances, some under our control, and some not.
Just look at some of the recent hacks that have happened to phones. There are bad apps that look benign, apps that claim to protect you from virus infections but are really what are called “fake AV” and harm your phone instead, and even malware that infects application construction tools. I will get to some of the specifics in a moment. If you are in St. Louis on August 3, you can come hear me speak here about this topic.
Part of the problem is that the notion of “bring your own device” has turned into “bring your own trouble” – as corporate users have become more comfortable using their own devices, they can infect or get infected from the corporate network. And certainly mobile users are less careful and tend to click on email attachments that could infect their phones. But the fault really lies in the opportunity that mobile apps present.
For example, take a look what security researcher Will Strafach has done with this report earlier this year. He demonstrated dozens of iOS apps that were vulnerable to what is called a man-in-the-middle attack. These allow hackers to intercept data as it is being passed from your phone through the Internet to someplace else. At the time, his report grabbed a few headlines, but apparently, that wasn’t enough. In a more recent update, he found that very few of the app creators took the hint — most did nothing. He estimates that 18 million downloaded apps still have this vulnerability. Security is just an afterthought for many app makers.
Another issue is that many users just click on an app and download it to their phones, without any regard to seeing if they have the right app. Few of us do any vetting or research to find out if the app is legit, or if it part of some hacker’s scheme, and to do so really requires a CS degree or a lot of skill. Take the case of the “fake AV” app that infects rather than protects your phone. There are hundreds of them in the Google Play store. FalseGuide is another malware app that has been active since last November and infected more than two million users.
The Judy malware has infected between 8.5 million to 36.5 million users over the past year, hiding inside more than 40 different apps. DressCode initially appeared around April 2016 and since then it has been downloaded hundreds of thousands of times. Both look like ordinary apps that your kids might want to download and play with. Hackers often take legit apps and insert malware and then rename and relist them on the app stores, making matters worse.
Even the WannaCry worm, which was initially Windows-only, has been found in seven apps in the Google Play store and two in Apple’s App Store. Speaking of Apple, the malware XcodeGhost is notable in that it has targeted iOS devices and resulted in 300 malware-infected apps being created, although that malware infected Apple’s desktop development environment rather than the mobile phones directly.
So what can you do? First, make sure your phone has a PIN to lock its use, and if you have a choice of a longer PIN, choose that. There are still at least ten percent of users that don’t lock their phones. Having a PIN also encrypts the data on your phone too.
Next, use encrypted messaging apps to send sensitive information, such as Signal or WhatsApp. Don’t trust SMS texts or ordinary emails for this.
Use a password manager, such as Lastpass, to store all your passwords and share them across your devices, so you don’t have to remember them or write them down.
When you are away from your home or office network, use a VPN to protect your network traffic.
Don’t automatically connect to Wi-Fi hotspots by name: hackers like to fool you into thinking that just because something is named “Starbucks Wi-Fi” it could be from someone else. Apple makes a Configurator app that can be used to further lock down its devices: use it.
Turn off radios that aren’t in use, such as Bluetooth and Wi-Fi.
Don’t do your online banking — or anything else that involves moving money around — when you are away from home.
Don’t let your kids download apps without vetting them first.
Turn on the Verify Apps feature, especially on Android devices, to prevent malicious or questionable apps from being downloaded.
Keep your devices’ operating systems updated, especially Android ones. Hackers often take advantage of phones running older OS’s.
I realize that this is a lot of work. Many of these tasks are inconvenient, and some will break old habits. But ask yourself if you want to spend the time recovering from a breach, and if it is worth it to have your life turned upside down if your phone is targeted.
:format(webp)/cdn.vox-cdn.com/uploads/chorus_image/image/68526858/FB_ATT_Prompt.001.5.png) This week, Apple announced the availability of iOS version 14.5 for its smartphones and tablets. The release contains an update that is a major change in direction and support for digital privacy. If you are concerned about your privacy, you should take the time to do the update on your various devices. Earlier iOS versions had the beginnings of this anti-tracking feature. If you go to Settings/Privacy/Tracking, you can turn off this tracking or selectively enable it for specific apps. When you install a new app, you will get a popup notification asking you about which tracking features you wish to grant the new app.
This week, Apple announced the availability of iOS version 14.5 for its smartphones and tablets. The release contains an update that is a major change in direction and support for digital privacy. If you are concerned about your privacy, you should take the time to do the update on your various devices. Earlier iOS versions had the beginnings of this anti-tracking feature. If you go to Settings/Privacy/Tracking, you can turn off this tracking or selectively enable it for specific apps. When you install a new app, you will get a popup notification asking you about which tracking features you wish to grant the new app.
 In this, the first of a two part series, I talk about why you want a BYOD program at your company.
In this, the first of a two part series, I talk about why you want a BYOD program at your company. Lisa Seacat DeLuca is the most prolific female inventor in IBM’s history. With more than 400 patent filings, she comes up with a new idea almost every week. She’s had numerous jobs within IBM and currently works as an omnichannel strategist for IBM Commerce. She works from her home-based Baltimore lab, which is filled with lots of different gadgets, including a 3-D printer.
Lisa Seacat DeLuca is the most prolific female inventor in IBM’s history. With more than 400 patent filings, she comes up with a new idea almost every week. She’s had numerous jobs within IBM and currently works as an omnichannel strategist for IBM Commerce. She works from her home-based Baltimore lab, which is filled with lots of different gadgets, including a 3-D printer.
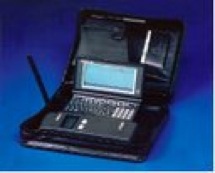 My first brush with wireless messaging was when Bill Frezza stopped by my office and gave me one of his first prototypes of what would eventually turn into the BlackBerry. It was called the Viking Express, and it weighed two pounds and was a clumsy collection of spare parts: a wireless modem, a small HP palmtop computer running DOS, and a nice leather portfolio to carry the whole thing around in.
My first brush with wireless messaging was when Bill Frezza stopped by my office and gave me one of his first prototypes of what would eventually turn into the BlackBerry. It was called the Viking Express, and it weighed two pounds and was a clumsy collection of spare parts: a wireless modem, a small HP palmtop computer running DOS, and a nice leather portfolio to carry the whole thing around in.