Writing a computer-themed column appearing today can be a tough assignment. But I want to assure you that first, it isn’t any net-fueled prank and second, that it is actually written from start to end by me and not by some algorithm. More on that in a moment.
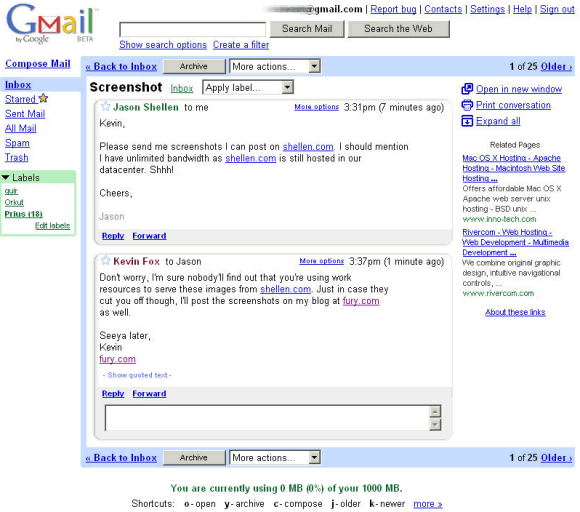
Today marks the 20th anniversary of Gmail’s creation. Google was playing with fire when it first announced the service in this press release, and the initial reaction was disbelief because of the date. Back then, it was an amazing feat to offer a gigabyte of storage — since expanded to 15 GB for the free tier. This was when many email services had capacity limits of 4MB or so, which seem laughable by today’s standards.
and the ability to search your entire email corpus. Now there are more than 1.5B users around, including myself. (I actually host my domain with Google, which was free until recently.) Here is a screen grab of what it looked like back then.
But there is another and sadder moment that I want to mention.
Over the weekend we lost one of the Great Ones, Dan Lynch, who was the founder of the Interop trade show. He was one of the prime movers behind the commercialization of the internet, back when we all used the capital “I” as befitting its status in society.
I was involved in the show in numerous ways: as a tech journalist (and editor-in-chief of what would become the leading computer networking business publication), as an editorial consultant to help guide the conference program, and as a speaker and lecturer. At its height, Dan put on five shows yearly around the world, and I spoke at many of them. Here is an interesting historical plot of when and where the shows took place.
You can read more about Dan’s accomplishments with this NYT obit written by Katie Hafner. He was 82, from kidney failure.
One of the features of Interop was its ability to force vendors into improving their products in real time, during the several days that the show was running, with what eventually was called the Shownet. In the early days, TCP/IP was still very much an experimental set of protocols and had yet to become the global lingua franca that it is today. The Shownet was born out of the necessity to get better interoperability, hence the show’s name. It began with 300 vendors and eventually blossomed to attract tens of thousands of attendees. This year the show is back from being virtual and being held in Tokyo this summer.
“The Shownet was also often the first place where many router or switch devices ever met a complex topology,” wrote Karl Auerbach, one of the many volunteer engineers who worked on it over the years, “Few saw the almost continuous efforts, done under Dan’s watch, between shows to design, pre-build (in ever larger warehouses), ship, deploy, operate, and then remove. The Shownet trained hundreds of electricians in the arts of network wiring over the years.”
I wanted to talk to Dan as part of an article that I am writing for the Internet Protocol Journal about the history and tenacity of the Shownet, but sadly we weren’t able to connect before his passing. He was truly a force of nature, a force that brought a lot of goodness to the world, and changed it for the better. Many of us owe our career developments, knowledge about computing, and human connections to Dan’s efforts.
So one final note. I came across this coda that explains “human-generated content” on a website by displaying one of three icons. I want to assure you that my website, newsletter, and any work that I produce is 100% written by me, that the people I quote are also actual carbon-based life forms, and no GPUs have been harmed or otherwise employed to produce this work product.

 I had a chance to speak to Janey Brummett who has spent three decades working in the IT department for the Catholic Health Association, the national leadership organization of the Catholic health ministry, representing the largest nonprofit providers of health care services in the nation. She came to the association as a paralegal who got an early taste for computers, back when PCs were first coming into businesses and when she was helping to spec out mainframe systems. “I was the conduit to talk to the programmers back then,” she said. Over the years she worked her way up the IT org chart until retiring this year in a position that most of us would characterize as the CIO.
I had a chance to speak to Janey Brummett who has spent three decades working in the IT department for the Catholic Health Association, the national leadership organization of the Catholic health ministry, representing the largest nonprofit providers of health care services in the nation. She came to the association as a paralegal who got an early taste for computers, back when PCs were first coming into businesses and when she was helping to spec out mainframe systems. “I was the conduit to talk to the programmers back then,” she said. Over the years she worked her way up the IT org chart until retiring this year in a position that most of us would characterize as the CIO. Not many chief security officers will point out not one but two times they took a job while their companies were under attack. But this is what happened to Jaya Baloo, who is now chief security officer at cybersecurity provider Rapid7 Inc. Even more interesting, she considers both times — which happened at two different companies — career highlights. She has a lot more to say in
Not many chief security officers will point out not one but two times they took a job while their companies were under attack. But this is what happened to Jaya Baloo, who is now chief security officer at cybersecurity provider Rapid7 Inc. Even more interesting, she considers both times — which happened at two different companies — career highlights. She has a lot more to say in  Erica Wilson has had many career transitions “but I’d have to say taking on a CISO role was certainly a good experience. I learned a LOT about myself and why having a people-first mindset – supporting their wellbeing and growth — needs to be critical for all organizations. By doing so, with a small but mighty team we were able to accomplish some amazing things.”
Erica Wilson has had many career transitions “but I’d have to say taking on a CISO role was certainly a good experience. I learned a LOT about myself and why having a people-first mindset – supporting their wellbeing and growth — needs to be critical for all organizations. By doing so, with a small but mighty team we were able to accomplish some amazing things.” Gayle Barton remembers the first time she wrote a purchase order for $75,000 worth of desktop computers when she was at St. Lawrence University. “It was probably three times my annual salary at the time and was quite exciting.” She got a handle on things since then: “For several jobs I changed the desktop purchasing process from ‘everybody gets what they want,’ with all the attendant complications of ordering, configuring, delivering, and training, to a standardized system. People got four choices: laptop or desktop, Mac or PC, with exceptions for people who genuinely needed something else. We saved hundreds of person-hours and much angst every year.” She developed the first web pages at one university “at a time when the dining hall menu, the bus schedule, the weather and the campus directory were the most popular pages. We gradually moved into helping with digital storytelling for both faculty and students and marrying databases to the web.” Gayle also remembered picking her university’s domain name with the director of operations. “We knew we weren’t the right people to choose this but no one else would understand or care, so we just had a laugh and went forward. Our first user was a math professor who messaged his family in Israel.”
Gayle Barton remembers the first time she wrote a purchase order for $75,000 worth of desktop computers when she was at St. Lawrence University. “It was probably three times my annual salary at the time and was quite exciting.” She got a handle on things since then: “For several jobs I changed the desktop purchasing process from ‘everybody gets what they want,’ with all the attendant complications of ordering, configuring, delivering, and training, to a standardized system. People got four choices: laptop or desktop, Mac or PC, with exceptions for people who genuinely needed something else. We saved hundreds of person-hours and much angst every year.” She developed the first web pages at one university “at a time when the dining hall menu, the bus schedule, the weather and the campus directory were the most popular pages. We gradually moved into helping with digital storytelling for both faculty and students and marrying databases to the web.” Gayle also remembered picking her university’s domain name with the director of operations. “We knew we weren’t the right people to choose this but no one else would understand or care, so we just had a laugh and went forward. Our first user was a math professor who messaged his family in Israel.”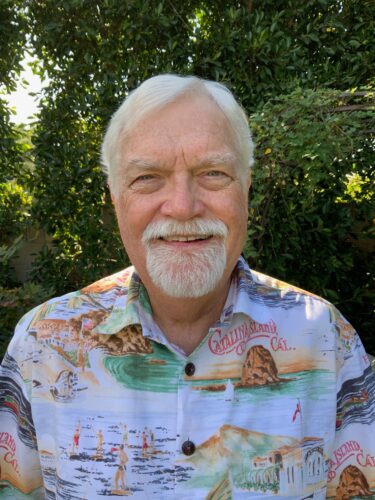 Terry Evans said:
Terry Evans said: Jerry Hertzler
Jerry Hertzler  Adam Kuhn
Adam Kuhn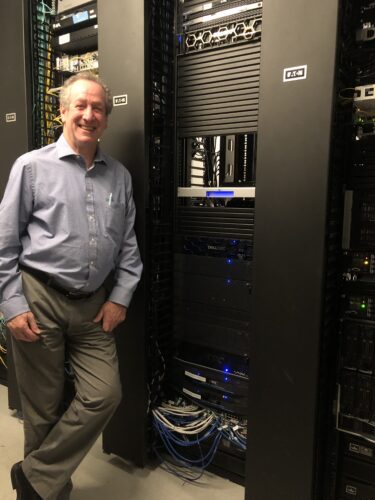 Sam Blumenstyk
Sam Blumenstyk Qualys’ annual security conference returned to a live-only event this week at the Venetian Hotel in Las Vegas, and the keynote addresses started things off on a very practical note… about selling coconuts, toasters, and carbon monoxide detectors. The first two keynotes featured speeches from both Shark Tank celebrity businessman and CEO of Cyderes, Robert Herjavec, and Qualys’ President and CEO, Sumedh Thakar. Both spoke around the similar theme of qualifying and quantifying digital cyber risks.
Qualys’ annual security conference returned to a live-only event this week at the Venetian Hotel in Las Vegas, and the keynote addresses started things off on a very practical note… about selling coconuts, toasters, and carbon monoxide detectors. The first two keynotes featured speeches from both Shark Tank celebrity businessman and CEO of Cyderes, Robert Herjavec, and Qualys’ President and CEO, Sumedh Thakar. Both spoke around the similar theme of qualifying and quantifying digital cyber risks.